Dynamic Malware Analysis
LetsDefend
Which of the following tools is different from the others in terms of its function?
A) Procmon
What activities cannot be viewed with Procmon? A) Syscalls
Which of the following tools does not provide hash information of files? A) Procmon
What is the Network configuration that provides Internet access through the network interface of the host operating system?
A) NAT
What name should a registry key be created to disable the ASLR feature?
A) MoveImages
Which tool should be used to detect network activities? A) Fiddler
What command should be typed in the “Run” application to switch to the “temp folder”. A) %temp%
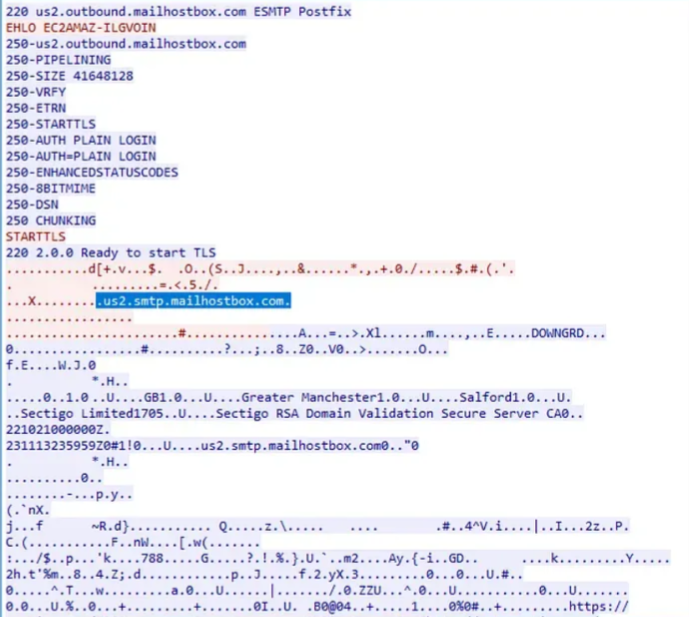
What is the domain name that the malware connects to for data hijacking?
A) us2.smtp.mailhostbox.com
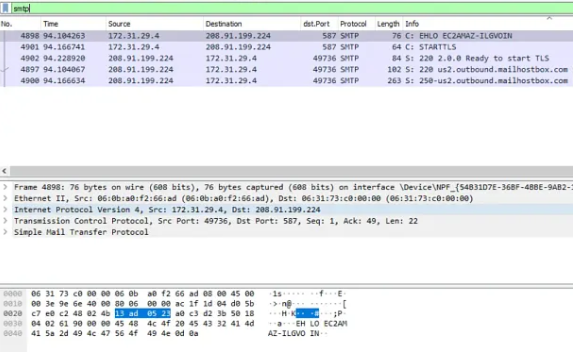
(Desktop/Malware Samples/law.exe) Connect Virtual Machine via ‘Connect’ Button. On which port does the malware communicate over?
A) 587
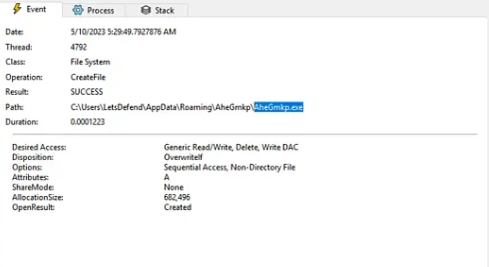
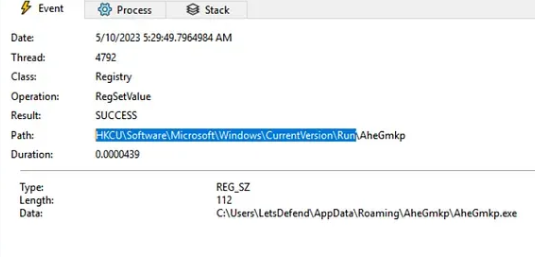
(Desktop/Malware Samples/law.exe) Connect Virtual Machine via ‘Connect’ Button. What is the name of the executable file that the malicious application writes to the AppData directory?
A) AheGmkp.exe
(Desktop/Malware Samples/law.exe) Connect Virtual Machine via ‘Connect’ Button. Which Registry Key does the malware use to ensure persistence?
A) HKEY_CURRENT_USER\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN
(Desktop/Malware Samples/payment advice.exe)(Password:infected) Connect Virtual Machine via ‘Connect’ Button. What is the domain name of the web application that the malware is requesting to learn its IP address?
A) checkip.dyndns.org

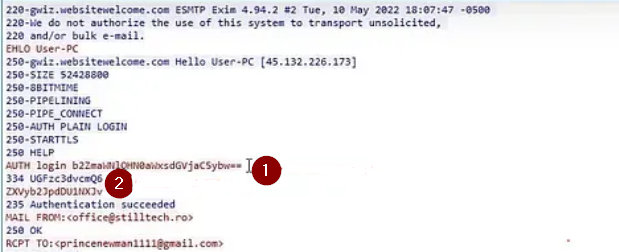
(Desktop/Malware Samples/payment advice.exe) What is the domain name that the malware connects to for data hijacking?
A) mail.stilltech.ro
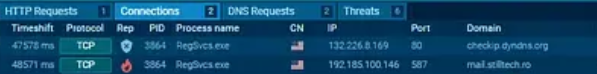
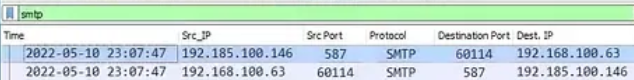
(Desktop/Malware Samples/payment advice.exe) What port does the malware communicate over?
A) 587
(Desktop/Malware Samples/payment advice.exe) What is the username used by the malware to authenticate to the mail server it connects for data hijacking?

(Desktop/Malware Samples/payment advice.exe) What is the password that the malware uses to authenticate to the mail server it connects for data hijacking?
A) eurobit555ro