
Investigate Web Attack
LetsDefend
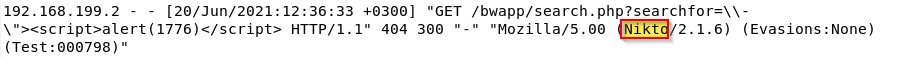
Which automated scan tool did attacker use for web reconnaissance?
A) Nikto
After web reconnaissance activity, which technique did attacker use for directory listing discovery? A) Directory Brute Force
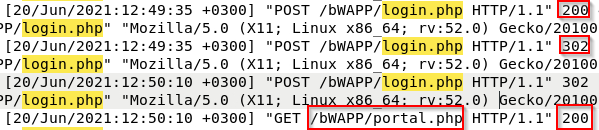
What is the third attack type after directory listing discovery? A) Yes

Is the third attack successful?
A) Yes
What is the name of fourth attack? A) Code injection
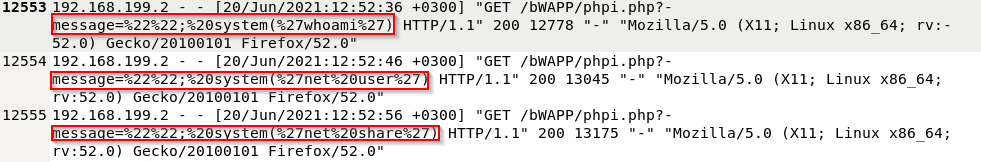
What is the first payload for 4th attack? a)whoami
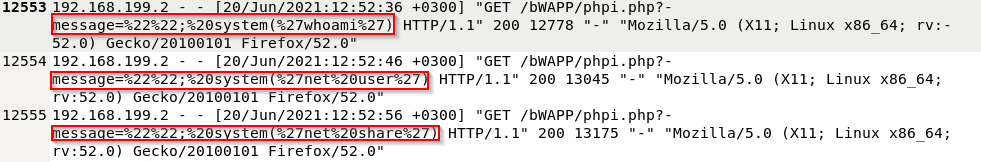
Is there any persistency clue for the victim machine in the log file ? If yes, what is the related payload? A)%27net%20user%20hacker%20Asd123!!%20/add%27