
Siem Alerts
LetsDefend
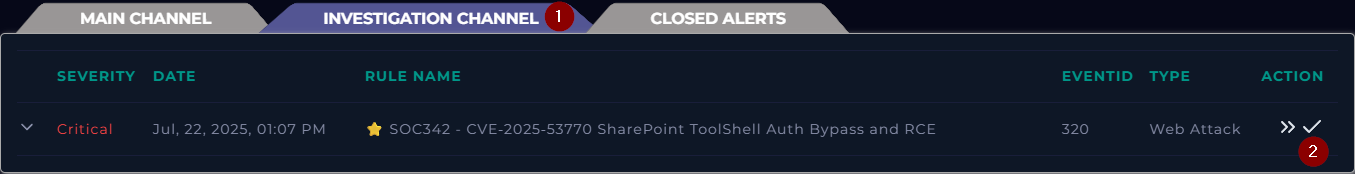
In which channel can you take ownership of the alert?
A) Main Channel
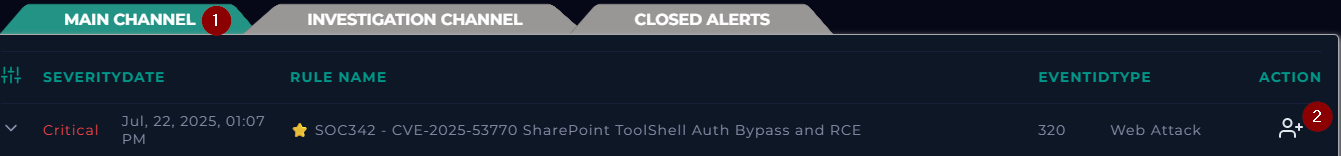
Once you have completed the analysis of an alert, in which channel can you close the alert?
A) Investigation channel
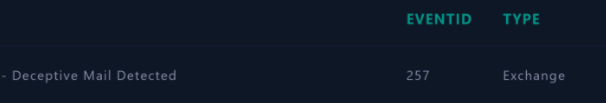
What is the “type” of the alert?
A)Exchange
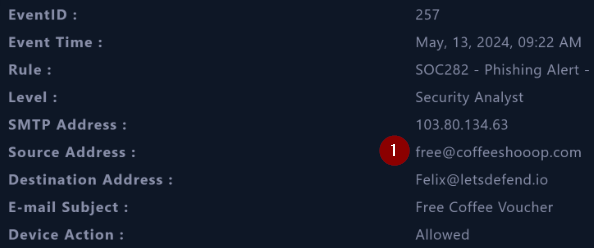
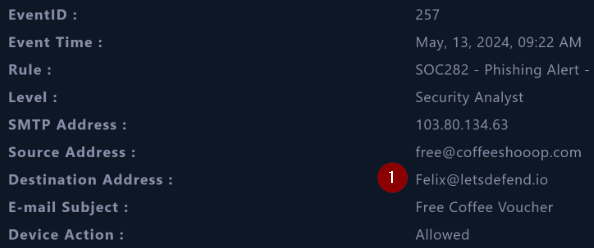
When was the alert generated?
A) May,13,2024, 09:22 AM
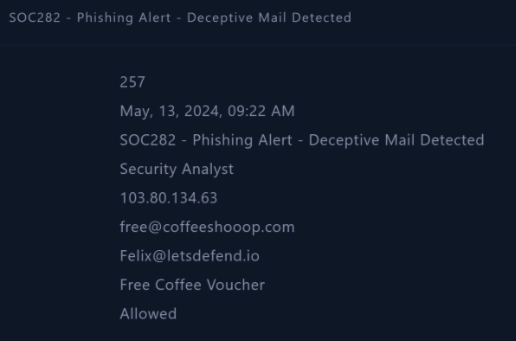
What is the email’s SMTP address?
A) 103.80.134.63

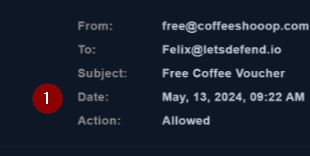
What is the source address?
What is the destination address?
Question: What is the name of the attachment?
Answer Format: filename.extension
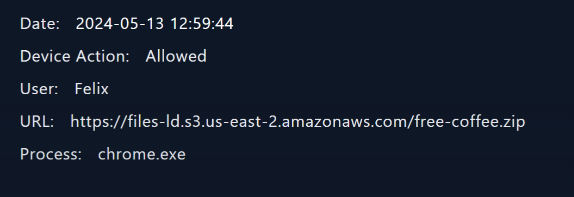
A) free-coffee.zip

What is the subject of the email?
A) Free Coffee Voucher
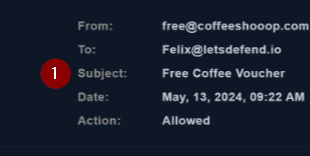
When was the email sent?
A) May, 13, 2024, 09:22 AM
Question: What is the IP address of the Felix host?
A) 172.16.20.151
When exactly did Felix download the malicious file?
A) May, 13, 2024, 12:59 PM
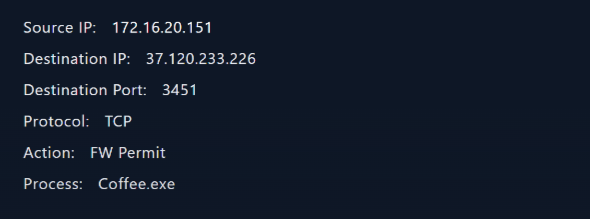
What is the C2 address?
A) 37.120.233.226
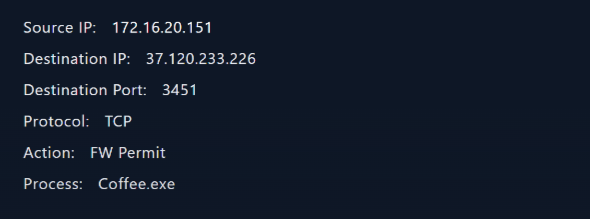
What’s the name of the process that communicated with C2?
A) Coffee.exe
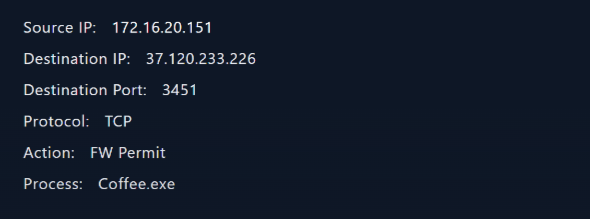
What port did the malware use to communicate?
A) 3451
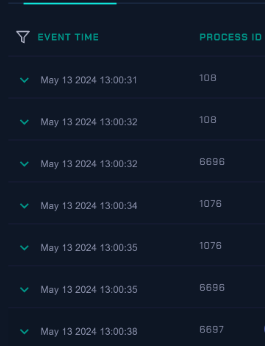
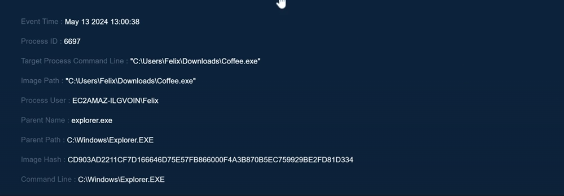
Question: What is the Process ID (PID) of the “coffee.exe”?
A) 6697
What is the “image hash” of the malicious process?
A) CD903AD2211CF7D166646D75E57FB866000F4A3B870B5EC759929BE2FD81D334
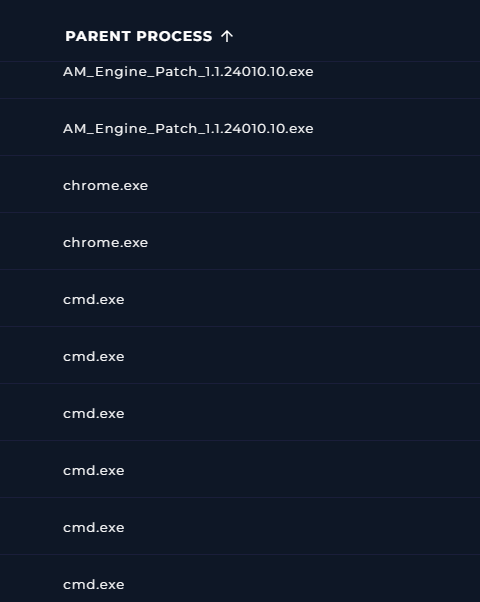
How many child processes does “cmd.exe” have?
A)7
On the monitoring page, through which channel can you access the official incident report of an alert?
A) Closed Alerts