Takedown
HTB
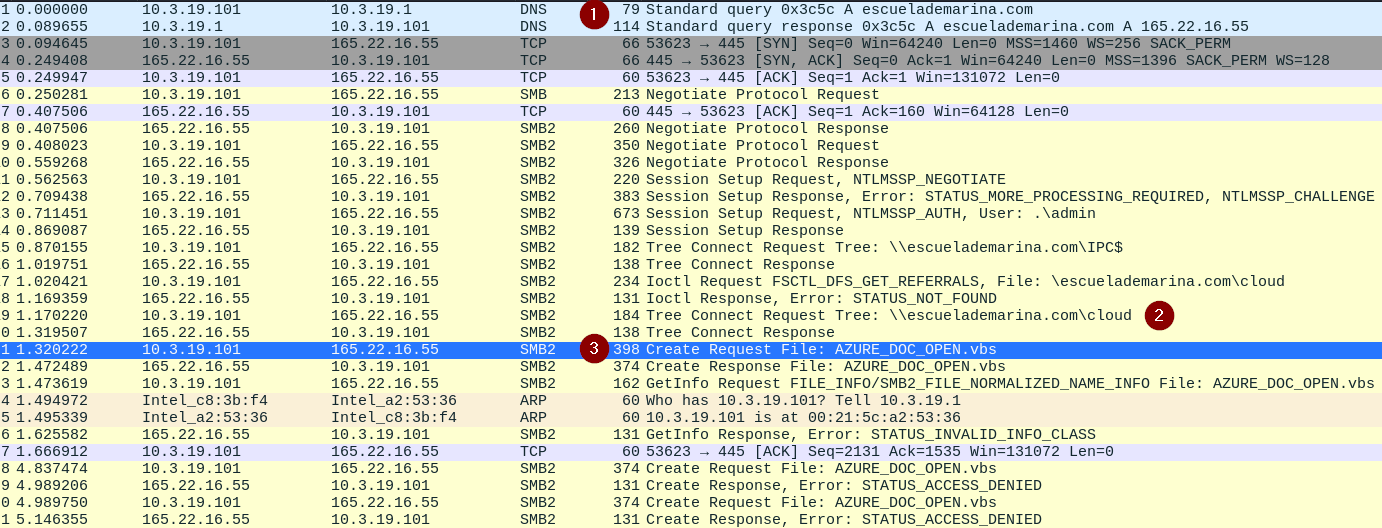
From what domain is the VBS script downloaded?
A) escuelademarina.com
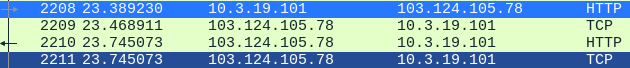
What was the IP address associated with the domain in question #1 used for this attack?
A) 165.22.16.55

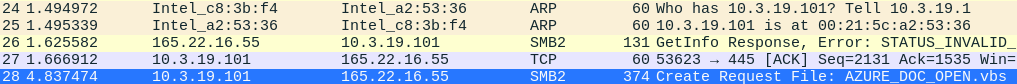
What is the filename of the VBS script used for initial access?
A) AZURE_DOC_OPEN.vbs
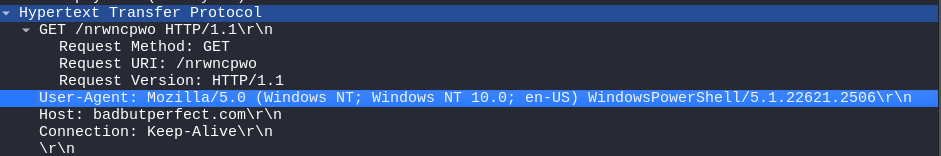
What was the URL used to get a PowerShell script?
A) badbutperfect.com/nrwncpwo
What likely legit binary was downloaded to the victim machine?
A) AutoHotkey.exe
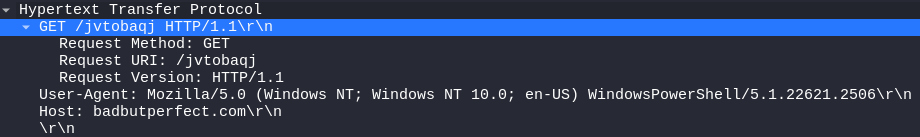
From what URL was the malware used with the binary from question #5 downloaded?
A) http://badbutperfect.com/jvtobaqj
What is the TLSH of the malware?
A)T15E430A36DBC5202AD8E3074270096562FE7DC0215B4B32659C9EF16835CF6FF9B6A1B8
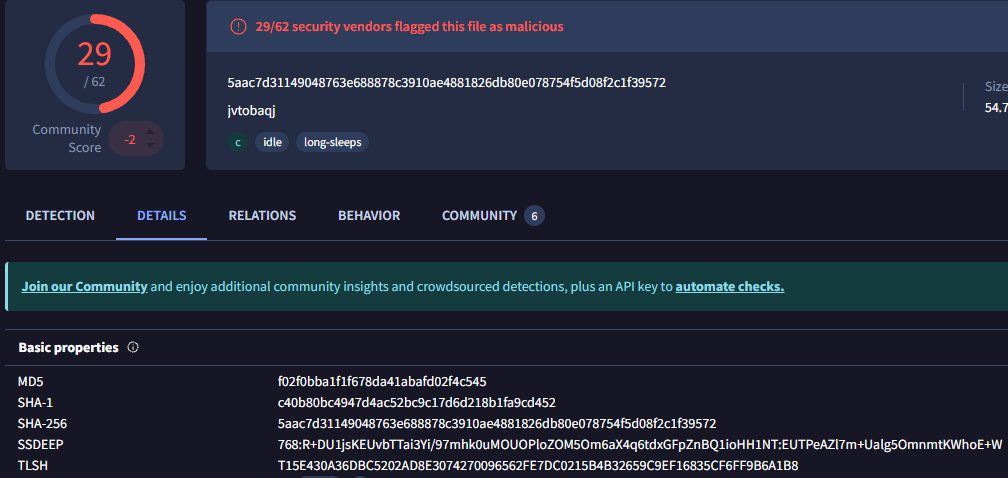
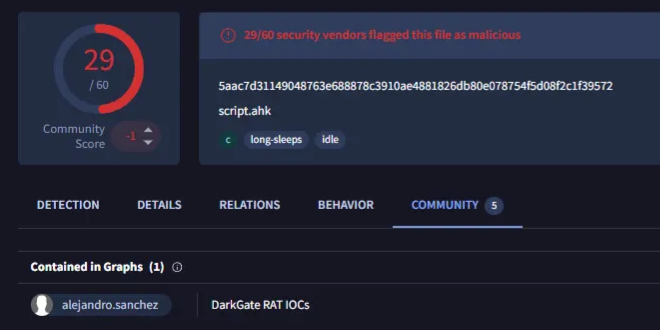
What is the name given to this malware? Use the name used by McAfee, Ikarus, and alejandro.sanchez.
A) DarkGate
What is the user-agent string of the infected machine?
A) Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/118.0.0.0 Safari/537.36
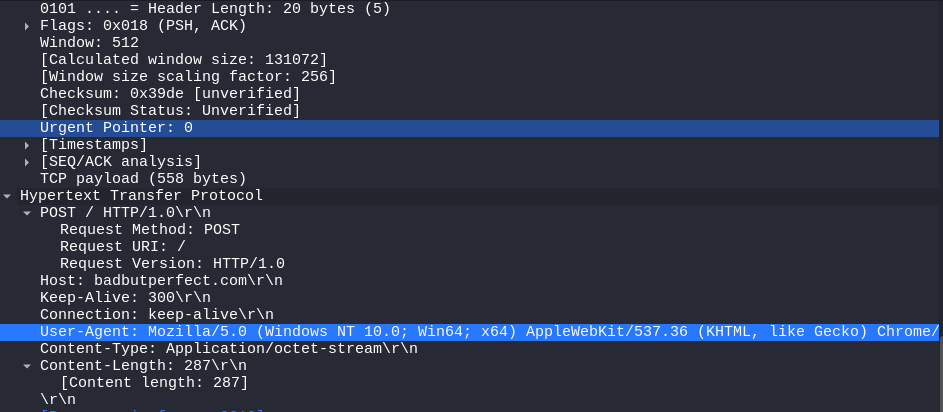
To what IP does the RAT from the previous question connect?
A) 103.124.105.78